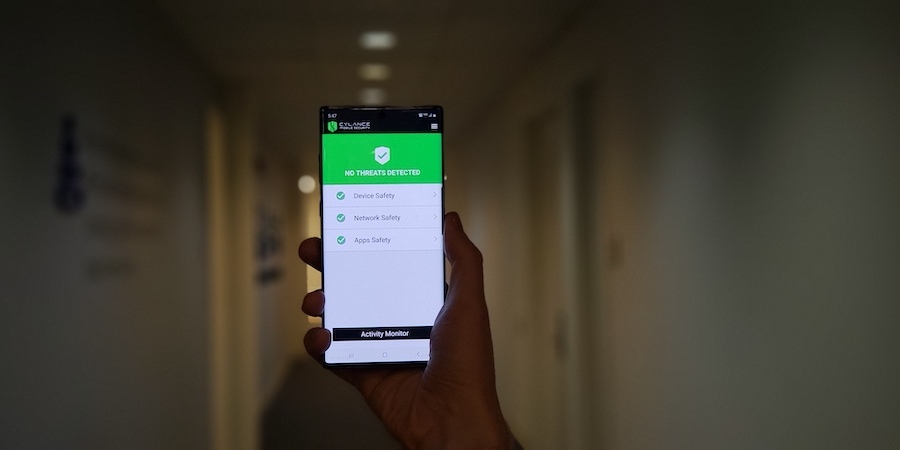
Cylance, a leader in cybersecurity, is bringing their lightweight, AI-driven protections to Android smartphones, including a partnership with Samsung meant to help bring awareness to the mobile device threat landscape. I spoke with Cylance’s Senior Vice President and GM Christopher Bray about the evolving threat environment and how the antivirus software provider is built to help address the devastating reality that no computing device is safe from the global pandemic of cyber crime.
More Than Antivirus
Q: While antivirus is a term used to describe some of the earliest standalone security software, it seems like what you have developed in Cylance Smart Antivirus is something entirely different from those early applications. How does it differ?
Christopher Bray: Those early programs were written to address the problem of the day. This product was developed to protect against the much more diverse set of problems we have now and into the foreseeable future. In the early days, very few viruses were being written, and their objective was mischief. Hackers back then were essentially pranksters. There were far fewer computing devices, with much less power, and they weren’t connected to high speed connections all the time. Every one of those dimensions is bigger, faster and presenting almost no friction to the spread of a virus or other threat. The more general term we use now is “malware” because there are so many ways that bad actors are combining bits of code, information and other data.
Why You Need an Incident Response Playbook
Get this free guide on how to respond to mobile security breaches — or thwart them altogether. Download Now
Q: It also seems like this malware isn’t just the work of pranksters. Serious money is involved, right?
Bray: Exactly. Today they are being developed by large, powerful organized crime syndicates, military cyberwarfare units and enemy governments. They have huge resources and employ large numbers of talented developers to construct sophisticated attacks. The only way to protect yourself and your business from this sort of threat without spending extraordinary resources is to take an AI approach to security, including having as much automation as possible. You don’t want to have to try and stay just one step ahead of these bad actors, because they are moving very quickly.
Future-Proof Cybersecurity
Q: How does Cylance keep up? It still requires regular upgrades and patches, right?
Bray: Cylance has a very different approach. Antivirus has historically been written to identify known viruses, essentially creating and maintaining a blacklist of code that it will quarantine when matches are found. Estimates suggest that 350,000 new exploits are being written every day. Even under ideal circumstances, the time it takes to identify the bad code, update the list of items that people need to be protected from and then distribute that list can take days. This “detect and respond” approach can no longer keep up. The Wannacry Ransomware attack in May 2017 had spread to hundreds of thousands of computers in a matter of hours. No Cylance-protected computer was infected by Wannacry. Even though it was entirely new malware, the Cylance protection running on each device recognized it as malicious code. According to SE labs report, Cylance would stop any malicious software that might be developed over the next 25 months — without any updates needed.
Q: Explain this in simpler terms, if you can. Are you saying that Cylance can protect files and apps from viruses that haven’t been written yet?
Bray: Essentially, yes. We like to say we can protect you from tomorrow’s threats today, while our legacy competitors can only protect you from yesterday’s threats tomorrow. Our approach does not rely on signatures or blacklists. Rather we rely on an algorithm that is trained on billions of samples of good and bad software, which has the ability to analyze millions of attributes of software and quarantines malware before it has the ability to execute. It’s the difference between prevention versus detect and respond. Exploits are evolving in type and complexity at an astonishing rate, but that report suggests today’s algorithm can protect against malware that hasn’t even been created yet — up to 25 months on average into the future. Also, our solution protects immediately upon installation, without needing to configure, update, scan or reboot. And the footprint is a fraction in size versus legacy solutions that require updates and signatures, and it has no noticeable impact on system performance. We continually train our algorithm and push out an update only when we feel the increased intelligence warrants it — which usually is somewhere between nine and 12 months. And when we do, it’s only a couple of megabytes and it happens automatically in the background, ensuring our users always have the latest version without having to configure or update anything themselves.
Do I Need Antivirus on My Smartphone?
Q: So far, most of the exploits have targeted computers, servers and infrastructure. Do I need antivirus on my smartphone?
Bray: It’s a fair question, and the answer is yes. Clearly we started by protecting Windows and MacOS computers because that’s where we saw the greatest threat. Currently we are seeing a growth in exploits involving mobile users clicking on a link in an email that launches malicious code, or apps that pretend to be something harmless, but actually do nefarious things in the background. The emails are made to look like they come from a known entity. On a mobile device, a user is five to 20 times more likely to be fooled by that email and click on the dangerous link. This is especially a problem in small and midsize businesses. Large organizations are more likely to have multiple layers of protection like enterprise mobility management (EMM) and virtualization, and the staff to configure and manage those tools. Small business needs a smart antivirus that manages itself.
Q: Does Cylance replace all of those other security tools? I’m sure everyone would like to have one tool for total protection.
Bray: Every size organization needs to have the appropriate approaches to secure their computing devices and the information on them. The customers that most appreciate the simplicity of Cylance Smart Antivirus, the small size of the application and our automatic AI-driven protection are smaller businesses. Most of our customers are business leaders in organizations too small for a full IT or security staff that can monitor and configure a range of security applications like advanced EMM or unified endpoint management (UEM). If you have fewer than 50 employees, you don’t have anyone on staff that can keep up with cybersecurity. For larger businesses, we recommend our Enterprise solution, Cylance Protect. But that requires experienced and dedicated IT staff to deploy and configure.
We partnered with Samsung because we think the combination of our software with Samsung Knox is a perfect way for small business to protect the devices, the data and the applications that their business and their users need, in a way that doesn’t require them to learn a whole set of new capabilities. Google, Samsung and Cylance are all working to contain malicious code so users don’t have to worry about it, but, especially for a small business, you want to have all three working together to ensure nothing gets through.
Stop threats before they occur. Get a four-month free trial of BlackBerry’s Cylance mobile security software when you buy Samsung Galaxy phones or tablets.