Posts by
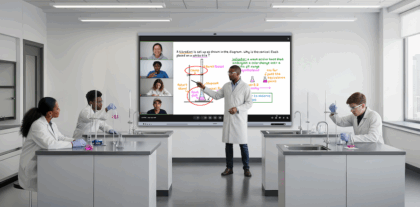
Samsung for Business
A global leader in enterprise mobility and information technology, Samsung offers a diverse portfolio of business technologies from smartphones, wearables, tablets and PCs, to digital displays and storage solutions. We are committed to putting the business customer at the core of everything we do, serving diverse industries including education, finance, government, healthcare, hospitality, public safety, retail and transportation. Follow Samsung for Business on Twitter: @SamsungBizUSA