In a world where the workforce is becoming increasingly mobile, making sure you have a plan in place to maintain corporate security is vital. Based on new research by NetEnrich, 68 percent of corporate IT professionals list “ensuring their organizations don’t experience breaches or attacks” as one of the top goals of their enterprise mobility security plans.
However, putting a plan in place is only the first step you need to take. As you give your employees more freedom around how and where they work, it’s also vital to make sure that you fully implement your plan in order to ensure the safety of your employee and customer data.
The NetEnrich research surveyed 151 corporate IT decision makers at companies in the U.S. ranging from under 100 employees to over 10,000. While almost 50 percent of respondents said they were managing fewer than 500 mobile devices, a sizable proportion (14 percent) were managing 5,000 or more — indicating the scale of the challenge some companies face in securing their mobile devices.
Implications of the BYOD Movement
One of the biggest challenges facing corporate security teams is managing devices like smartphones and tablets that are used by employees both for work and personal use. The bring your own device (BYOD) phenomenon has led to a radical change in the way companies deal with enterprise mobility. In many companies, this trend has been accelerated from the top, with C-suite executives looking to use devices that offer a much more feature-rich experience.
The problem for corporate IT teams is how to keep sensitive corporate data secure while at the same time allowing employees to access their personal email, messaging and apps. “The proliferation of mobile devices can undermine enterprise network security in the absence of effective security policies and provisions,” warns a report from Juniper Networks. “The biggest challenge related to mobile device proliferation is how to accommodate all of the different users, many of whom have multiple devices running a variety of different applications as they connect to the enterprise network in different ways at different times and from different locations.”
The Mobile Security Evolution
This eBook outlines the keysteps to help align business needs with mobile security. Download Now
Enterprises Must Prepare for a Wide Variety of Attacks
As workers migrate away from a fixed desktop location where all their work is done, those seeking to attack corporate networks are similarly shifting their focus from desktop operating systems to mobile operating systems. This means that enterprise mobility security plans need to be ready for a wide variety of attacks, including mobile malware, phishing attacks, data leaks and vulnerabilities in older versions of operating systems.
According to the NetEnrich survey, 45 percent of respondents said that mobile malware was the biggest cause of enterprise mobility attacks. Another major concern is the vulnerability posed by accessing public cloud services on phones, as the public cloud still isn’t sufficiently secure.
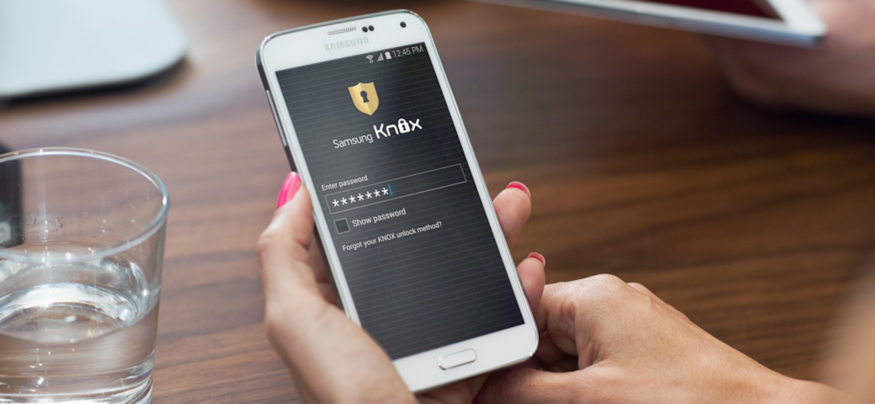
Highlighting the problem of using mobile devices for both work and personal use is the 42 percent of respondents who reported data leaks due to “cutting and pasting secure data to unsecured or public locations.” One of the most widespread methods of countering this specific threat is through containerization, or sandboxing. A secure data container is a mobile application used to separate and secure a portion of a device’s storage from the rest of the device. It essentially allows you to create a secure enclave within your device where you can store your most sensitive information and which cannot be accessed by apps or services that don’t have permission.
With solutions like Samsung’s Knox Workspace, this can all be managed remotely by the IT team, and it also allows them to wipe just the data within the secure container so that employees can continue using their smartphones or tablets after they’ve left the company.
Additional Security Methods
While containerization is an important part of an enterprise’s mobile security management plan, your strategy should also incorporate additional security measures like the use of two-factor authentication and a whitelist for approved apps that users can download to their devices.
According to the report from Juniper Networks, “It is necessary … to treat different devices differently, even for the same user, while giving all users a consistent and seamless connectivity experience, regardless of the device and access method used.”
As smartphones become a larger part of our everyday lives, a security awareness program for securing employees’ mobile devices is crucial for businesses.