The General Data Protection Regulation (GDPR) took effect in May. The content of the 99 articles may be too dense for easy digestion, but the principles are simple enough: people have a variety of privacy rights when it comes to their personal data, and anyone holding or processing that data is obligated to respect those rights.
The GDPR definition of personal data is pretty broad: “any information relating to [a person] who can be identified by a reference … such as a name, an ID number, location data, online identifier,” and so on. That means, for example, if you are collecting logs of web page accesses with IP addresses, you’ve got personal data on your servers.
In theory, US organizations are not required to comply, and it’s highly unlikely that the US will go as far as the EU has in recognizing and enforcing privacy rights. But many companies are interested in complying with GDPR so that they can do business with European customers.
IT managers of these organizations need to have a discussion with their teams about the risks that mobile devices pose to GDPR compliance, and the best strategies for dealing with them. Here are four places to start.
1. Be Careful of Overcollection
Mobile devices are excellent tools to have on retail floors, in the field and in kiosks. The temptation when you have a customer’s or client’s attention is to ask them a lot of questions and store the answers, because it couldn’t hurt to have all that information — could it?
In the world of GDPR, it could.
GDPR requires consent to collect personal data. And once you’ve collected it, you have to be very careful where you keep it (including what country the data is stored in), and you have to make it easy to erase, restrict how it’s used, and report on what you’ve stored. All that adds up to a big headache if you’ve “over-collected,” or taken data you don’t really need.
GDPR isn’t just for websites — it applies to any time you collect data. If you’re using mobile devices to collect data, review your applications and make sure you’re not collecting more data than you really need.
2. Watch for Mobile Device Loss
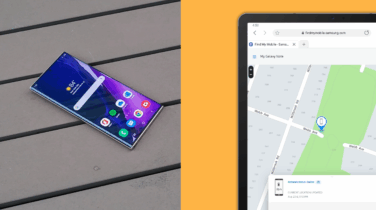
GDPR sets in motion a chain of costly and time-consuming events if you ever lose someone’s personal data. Obviously, you’re already thinking about this and about ways to minimize the risk of data loss. But don’t forget that mobile devices often have customer databases and other information on them — and this could qualify as personal data under GDPR. Misplacing a smartphone or having a tablet stolen could be an extremely expensive loss.
GDPR grants a pass if the data is encrypted, so make sure you’re maintaining any private customer data in an encrypted partition. Android has required full-disk encryption since version 6, although there is still an exception for devices that can’t handle the load and for removable SD Card storage slots. Slow devices are probably not an issue, but if you’ve added a microSD card to your device for additional storage, make sure it’s encrypted, either with on-device settings or using a policy in your Mobile Device Management (MDM) tool.
3. Protect the Portals
Another concern for personal data loss is unauthorized access. GDPR Article 25 requires that you “shall implement appropriate technical and organizational measures” to guard against unauthorized access. In the larger organizational context, this turns into an Identity and Access Management (IAM) question that requires controls above individual smartphones and tablets. But you should also look at your mobile device settings to be sure that you’re using the strongest authentication possible.
Build a BYOD Plan for Your Business
Get our comprehensive guide and template for developing a BYOD policy tailored to your organization. Download Now
For mobile devices, that means avoiding passwords and pushing towards biometrics for authentication — not just to the device itself but also for the application. Turning on biometric authentication on smartphones is easy — most now come with fingerprint readers, and high-end devices also include more advanced techniques such as iris scanning. Enabling applications for biometric authentication using smartphones and tablets is also simpler now, thanks to APIs such as FIDO.
Shifting to biometric authentication just for GDPR isn’t going to be an easy sell, but if you were looking for another reason why you should step up your authentication and authorization game, GDPR is another arrow in your quiver.
4. Mobile Security Doesn’t Change
The principles behind GDPR don’t change any advice you’ve already received on how to secure mobile devices. GDPR simply reinforces everything that most IT managers are already doing to secure mobile devices. Using features such as work/home profiles or containers, enforcing passcodes and device lock, and having a remote wipe policy are already in most IT managers’ playbooks for mobile device security.
GDPR doesn’t change any of that, and really doesn’t impose new specific requirements on protecting mobile devices. Instead, it’s an opportunity to double-check and double down on best practices you should already be using to secure and manage mobile devices.
Want more help revising your mobile policy to keep GDPR in mind? Get an in-depth look with our BYOD guide and template.