When it comes to cryptocurrencies and blockchain technology, the hype and hysteria are almost overwhelming. But hidden in the hyperbole is a valuable lesson in smartphone security.
What Is Blockchain? Introducing the Shared Ledger
Let’s start with Bitcoin, the oldest application of the blockchain. (Almost all cryptocurrencies work in the same or a similar way.) Bitcoin introduced the idea of a shared ledger, and people have since been increasingly eager to find applications for the technology. Meanwhile, cryptocurrencies based on the blockchain have become more and more popular.
Fundamentally, the blockchain solves an important problem with virtual money: the double-spending problem. In physical money, the problem is solved by exchanging bills and coins, but in virtual money, it’s all just bits moving around.
With all those bits flying everywhere, it’s especially important to keep the ledgers straight. Knowing who owns what money at any instant is key to keeping someone from spending the money twice. Traditionally, this is handled by banks — “trusted third parties,” in Bitcoin parlance — who make sure that any one set of bits is only in one place at a time. The biggest breakthrough in Bitcoin’s original design was solving the double spending problem without a trusted third party.
But if all the blockchain technology excitement is cleared away, that still leaves a big question: If blockchain is a shared ledger, what’s on the ledger?
The answer lies in the nature of Bitcoin transactions, which consist of small messages transferring coins from one user to another. These messages are cryptographically signed using standard public/private key technology. When one Bitcoin user sends coins to another Bitcoin user, they do so by writing a message in a particular format, and signing the message with the hash of the receiving user’s public key, using the sender’s public/private key pair.
The ledger records all of this. Later, the Bitcoin user that received the coins can send them to someone else by proving they have the private key that goes with the public key that was linked to the original transaction.
And that’s where security comes in. Because if you receive coins from someone, and if you lose the private key that went with the public key used to sign the transaction, then those coins are lost: you can’t prove that they’re yours and they sit in coin limbo — forever.
What’s the Impact on Smartphones?
It’s all about those private keys. If you lose them, you lose your coins. If someone steals your private key, they can steal your coins. Keeping the private key safe and away from the bad guys is a monumental concern for anyone using cryptocurrencies.
The Mobile Security Top 10
Download our guide to better securing the personal and work data on your mobile phone. Download Now
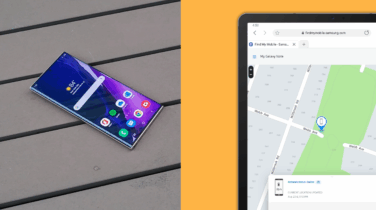
This is where wallets come in. Cryptocurrency wallets keep track of, among other things, the private keys associated with the virtual coins. Wallets come in many different forms, from online services to desktop applications to bits of physical hardware (and even pieces of paper) to smartphone applications.
Of these, smartphone-based cryptocurrency wallets are the best approach to short-term and medium-term storage — that is, “spending money,” the amount you might choose to carry with you in your real wallet. Meanwhile, long-term storage of cryptocurrency should be done with a backup (or several) of the private key, stored completely offline, and not on your smartphone — the same protection you might have for your personal savings account.
Comparing Cryptocurrency Storage Solutions
Why do smartphone-based wallets have an edge? It comes down to the Trusted Execution Environment (TEE) in the smartphone. The TEE is a separate execution environment with its own memory and persistent storage, completely isolated from the rest of the device. The Android OS can’t reach into the TEE, even if the former is completely compromised. The only way to get to and from the TEE is with an API that calls small applications running in the TEE “trustlets.” With a properly written wallet that uses trustlets to manage the keys, security is seriously tight.
If a wallet stores the private keys on a normal persistent store (such as a hard disk or SSD), whether on a standard Windows PC or in a smartphone, a bit of malware can easily get access to them. If those private keys are in the TEE and only accessible via a trustlet, there’s no possible way the malware can extract the keys directly. And with platforms like Samsung Knox that wrap additional protections on the TEE on top of the normal Android features, the keys are even better protected.
This is why smartphones have an edge over laptops and desktops for cryptocurrency wallets: without the benefits of the hardware-based TEE, the keys are more vulnerable. There is a significant caveat: a naïve wallet developer might choose to simply store the keys on the normal internal storage of the phone, in which case there’s little additional protection from using the smartphone platform. Or the wallet itself might be malware, in which case all bets are off. But with the right wallet leveraging the benefits of smartphone TEE, there’s no place safer to store your money.
Smartphones also edge out, from a convenience point of view, so-called hardware wallets — offline devices that look like USB drives or other disconnected protected storage. Although hardware wallets are the best choice for long-term cold (offline) storage of cryptocurrency, they lack the convenience of a local smartphone application, making them poorly adapted for frequent use.
Cryptocurrency users may not pay much attention to the mechanics of how their coins are stored, but that can be a dangerous attitude to have. Picking a dependable cryptocurrency wallet is an important part of using cryptocurrencies safely. Smartphones with enhanced Trusted Execution Environments provide the ideal platform for secure storage.
Learn more about how Samsung Knox’s defense-grade security makes Samsung phones the most secure available.