There is no question that in 2019, mobility is critical to a company’s efficiency, profitability and growth. At the same time, the use of mobile devices increases the business’ attack surface and extends the security risk.
From phishing scams to device theft, data breaches due to inadequate mobile security have become a real concern. According to Verizon’s latest Mobile Security Index, 83 percent of businesses say that their organization is at risk from mobile threats, and 86 percent agreed that mobile is the fastest-growing security threat.
Common Mobile Security Concerns
There are many ways that mobile security can be compromised. Some breaches are caused by devices that don’t have adequate built-in security controls, while others are the result of lax management or user error.
Verizon’s research shows that malware is the foremost mobile security concern for businesses, followed by phishing and ransomware. Network attacks related to use of unsecured public Wi-Fi are also a top concern, and rightly so. More than four out of five of employees admitted to using public Wi-Fi for work tasks, even if officially banned by their employer.
Why You Need an Incident Response Playbook
Get this free guide on how to respond to mobile security breaches — or thwart them altogether. Download Now
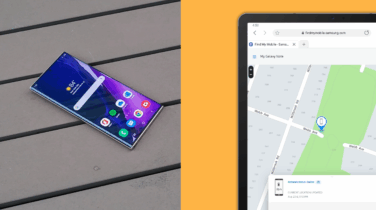
Employees may also lower the company’s defenses by creating weak passwords and failing to make password updates. This makes it easy for hackers to infiltrate the devices and access sensitive information, such as classified company data, text messages, emails and personally identifiable information (PII) or credentials. Device theft or loss is a particular concern, because if hackers are able to get past the lock screen, they have an open door to the company network.
In other cases, employees might download an application, assuming it’s safe, only to have that application introduce malware or spyware on their devices. With this nefarious code, it’s simple for hackers to steal sensitive information.
Don’t Let Security Fears Hold You Back
While mobile security threats are very real, there are ways to minimize the liability that mobile devices can cause. The best way to do this is by using a three-pronged approach that focuses on device security, policies and device management.
Device Security: When it comes to security features, not all mobile devices are created equal. Choose a security platform that is built directly into mobile devices, protecting it from attacks and continuously monitoring for suspicious activity. If it detects signs of tampering, a well-defended device can automatically shut down access to sensitive data or applications. A comprehensive security platform will also incorporate biometrics such fingerprint or iris scanning to restrict device access.
Policies: It’s surprising how many companies don’t have acceptable-use policies (AUP) for mobile devices. Implemented and communicated properly, an AUP can go a long way towards improving mobile security. Verizon found that more than half of organizations surveyed don’t have a comprehensive AUP covering the types of apps employees are allowed to install on their phone, Wi-Fi network usage or limits on personal use. Be sure to establish and regularly communicate policies around data and application use, public Wi-Fi, passwords and encryption. If your company allows employees to use their own devices for work purposes, create specific terms and conditions, such as use of secure containers for work information, virus and malware protection and two-factor authentication. Samsung provides a comprehensive guide to writing a BYOD policy and offers a template to get you started.
Management and Policy Enforcement: Developing policies is an important step, but enforcing them can be difficult. It’s much easier to enforce these policies with an automated approach through Mobile Device Management (MDM) or more comprehensive Enterprise Mobility Management (EMM) solutions. A comprehensive MDM/EMM solution allows companies to set policies and device settings; restrict use of device features such as cameras, screen capture and Bluetooth; allow or disallow use of public app stores; enforce encryption; determine which applications are allowed and which are blocklisted; require two-factor authentication; and set up secure containers on specific users’ devices.
With secure devices, solid policies and automated management and control, mid-sized companies can confidently move forward with mobility.
Take a free assessment to discover if you have the right mobile security plan for your business.