In this News Insight, Ars Technica explores the dangers posed by public access Wi-Fi, weak password protection, and the lurking coffee shop hacker. If you’re looking to bolster your enterprise security, explore the benefits of biometric authentication in this white paper. — Samsung Insights editorial team
Stop! You’re about to access an unsecured Wi-Fi network—so says the warning we’ve all encountered. At a coffee shop, waiting for a flight, even in city parks, it’s almost impossible not to find public Wi-Fi anymore. But many networks remain vulnerable, and still too many websites that collect user data eschew HTTPS, all leaving the door open for a thief to access people’s machines.
There’s plenty of ways to snatch people’s information right out of the air. YouTube returns almost four million results for “Wi-Fi hack,” videos with detailed instructions how to break into computers over unsecured networks. And the web’s full of easily downloadable applications that intercept packets exchanged between the router and computers—a process known as “sniffing.” These applications can be beneficial; they’re a great way to assess the health and vulnerabilities of a network. But if the data’s unencrypted, they provide an attacker easy access to rip sensitive information.
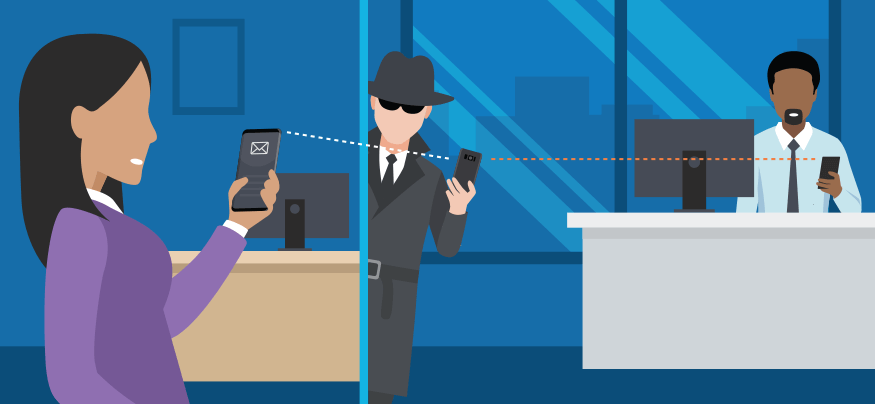
There are a number of doors an attacker might try. Weak password, default network configurations, and no additional security measure — all easily avoidable — are one. Sometimes attackers will try to crack the WEP or WPA encryption protocols, the standard security of web traffic (WEP has been deprecated but can still be found). Once between the targeted computer and the router, there are two basic snooping methods. Passive monitoring means a thief “eavesdrops” and doesn’t interfere with the data transfer. This is nearly impossible for company IT managers to detect.
The second category is active monitoring, where the thief generates, alters or disrupts communication. An attacker might change message contents between parties, impersonate a party to gain access to another network, or even hijack the machine for a denial of service attack, where they have the machine suffocate the network with data.
It’s important to point out, the number of people accessing insecure networks versus those who get their data sniffed, or their machine’s snooped, is extremely small. There aren’t that many attackers roaming around. And with modern fraud and digital payment protections, like TLS, the risk of getting financially wiped out is even smaller. Sometimes intercepted information can result in an attacker hijacking someone’s email to send hateful or scammy message — “Help, I’m stranded in London! Please wire me $1,000!” — but the real worry’s when an attacker has bigger plans.
To the chagrin of IT managers the world over, employees tend to use the same password across their digital account — which usually includes work accounts. So if a thief wants to get in a company network—their best point of entry may be a nearby coffee shop. They wait for someone with an employee badge from the targeted company to open their laptop while sipping their latte — and sniff their data.
The employee doesn’t have to access their work network for the thief to get what they want. If the employee accesses a non-HTTPS website — say, to purchase from a small online vendor — the thief could lift the employee’s password. If the employee uses that same password at work, the thief has a way in. These can result in “spoofing” attacks where a thief impersonates someone to lift sensitive data. Company IT managers take precautions like assigning employees usernames with random characters or requiring periodic password changes, but those practices are far from universal.
There’s a third method that’s of increasing concern in security communities: “rogue” Wi-Fi networks. An attacker will set up a network that mimics a network that someone thinks they recognize and trust; instead of “CompanyWiFi” the attacker creates “CompanyWiFi–5G”. Now they’re passing data straight through a malicious computer. An adept hacker could go a step further: mimic someone’s work VPN and set up a second VPN communication with the company. This lets the attacker become a “man in the middle,” with access to all information flowing between the two.
How to Thwart the Middle Man
Here are three tips to mitigate man-in-the-middle attacks and keep your data safe. Download Now
Rogue network attacks aren’t necessarily restricted to the technically naive. At the 2016 RSA conference, a gathering of the world’s top security experts, a group of presenters lured 2,456 attendees to join — or automatically connect to, as many devices will—to their fake network. Ryan Orsi, director of strategic alliances at WatchGuard Technologies and one of the presenters behind the test, says the vast majority of devices that logged on visited peer-to-peer file sharing sites, indicating they were probably accessing important documents.
“If we were the bad guys, we could have taken a number of actions to infiltrate these devices using known exploits, phish for login credentials or credit card data using bogus splash pages, or snooped for other sensitive data,” Orsi noted. “The data at risk is vast and includes keystrokes, usernames, passwords, credit card numbers, in short, anything entered on the connected device.”
Explore the possibilities of biometric authentication in this white paper.