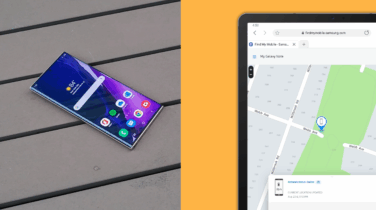
Smartphones and tablets have revolutionized workflows for businesses of every size, giving employees the ability to work from anywhere. Unfortunately, the information on those devices is not secured unless authentication measures have been put in place, meaning the freedom of being mobile carries with it significant risks of lost and stolen devices.
Some employees may resist the inconvenience of authentication protocols, but it should be considered a nonnegotiable requirement of using mobile devices in your business — and that includes you, by the way.
Luckily, you have many choices about how to authenticate a user’s identity. Gone are the days of requiring excessively long passcodes, making authentication a business-wide headache. With biometric authentication, users are now able to validate their identity with a fingerprint or facial recognition. Each method has limitations, advantages and disadvantages to consider.
Evaluating Biometric Authentication for Your Workplace
Biometrics and biometric authentication have evolved over several generations of technology. Government and military computers and access doors have used fingerprints and retinal scans for years, but the technology has matured to the point where it can be packed into a mobile device and can respond quickly and reliably. In general, security organizations such as the RSA suggest that sensitive information be protected by a multifactor authentication approach where biometric authentication is part of the access control solution.
Why You Need an Incident Response Playbook
Get this free guide on how to respond to mobile security breaches — or thwart them altogether. Download Now
For each biometric authentication method, the factors that should be considered include:
- False acceptance rate (FAR): Can someone get by the authentication if they aren’t actually the intended user? This is known as spoofing. Unless your business interests have no value, you don’t want to select a method that can’t be relied upon to deny inexact matches. You have better secure methods you can select from.
- False negatives: In a biometric system, a false negative is when the right person can’t get through. This is usually caused by environmental or contextual factors that make capturing reliable biometric information difficult. Most often this will include lighting, dirt or clothing that makes authentication more difficult. When making your choice, this is potentially where you have the most control. If the environment where your authentication need is at all predictable, start here for differentiating the methods. Consider whether your users are wearing gloves or eye protection, or will be using devices in harsh conditions.
- Speed to open: Authentication that takes more than a few moments will feel like an extraordinary burden to most users. Luckily this is an area where modern computing speeds have caught up to user attention spans enough to make wait times on certain authentication methods all but imperceptible.
- Ease of integration: Can the solution be added to interfaces and content types that are most important to your business? Device manufacturers and application developers that have any sort of security focus will likely support multiple approaches to accommodate the array of needs that most businesses have.
Facial Recognition
Facial recognition uses a camera or three-dimensional scan to read the face of the user. Faces are truly unique only to the degree that you capture the reference images and the scanned image in sufficient detail. Systems that use traditional camera images are relatively easy to spoof and are highly dependent on lighting and angle of capture.
Three-dimensional scanning of the face is more difficult to cheat, but this type of authentication also faces challenges, like recognizing people who change glasses or hats and requiring undivided attention from a user for at least a moment. For many knowledge-worker use cases, the user’s attention will be required anyway (to read an email, for instance). If the device is used in an industrial or emergency situation, on the other hand, looking at the device even for a second can be undesirable, if not disastrous.
Facial recognition is available on many of the most recent Samsung devices, including the Galaxy S10 and S10+ and the Galaxy Note10 and Note10+.
Iris Scanning
The iris is an extraordinarily complex part of the human anatomy, far more complex and unique than a fingerprint and much more available if you are wearing gloves. Originally, the complexity of iris scanning made it difficult to implement on mobile devices, but Samsung devices introduced the option in 2017.
The extremely low FAR rate for iris scanning comes at the slightest cost of time. There can also be some false negatives from glare or sunlight, but this is a good option for high security in manageable light conditions.
Iris scanning is available on the Samsung Galaxy S8, S8+, Note8, Galaxy S9, S9+ and Note9.
Optical and Capacitive Fingerprint Sensing
Most smartphones today leverage either optical or capacitive fingerprint sensing technology. Optical sensors work much like cameras, analyzing an image of the print to compare key markers and make a match. While better implementations incorporate antispoofing algorithms, optical technology can in some instances be fooled by a two-dimensional reproduction of a person’s print.
Capacitive sensors generally have lower FARs and won’t be spoofed by a two-dimensional reproduction. Instead of an image, they use an array of tiny capacitors to sense the ridges of the fingerprint in contact with the sensor. While more secure than the optical-based methods, capacitive sensors have been on rare occasions spoofed with fingerprint casts.
If optical or capacitive fingerprint sensors are used in conjunction with a second authentication factor, like a passcode (see below), they are a very secure method — but adding the second factor impacts usability.
Ultrasonic Fingerprint ID
Introduced in the Galaxy S10 and S10+ and the Galaxy Note10 and Note10+, ultrasonic fingerprint ID added greater security and convenience. Ultrasonic fingerprint sensors use ultrasonic waves to build a highly accurate 3D model of the print. The full contours of the fingerprint are used to authenticate — making it extremely difficult to spoof. The ultrasonic sensor can also be embedded behind the display, maximizing screen real estate.
Multifactor Authentication
Multifactor authentication (MFA) uses a combination of authentication factors to determine a user’s identity. Most commonly, two-factor authentication (2FA) is used as a combination of something you have (like a credit card) and something you know (like a PIN). In mobile devices, biometric authentication methods are referred to as inherent factors, as the biometrics inherently belong to the person whose identity is being verified.
MFA is most useful when you are securing highly privileged information or are trying to comply with specific regulations. Governments, the military and some high-security businesses have been using MFA for years, but mobile devices and biometric authentication on mobile devices have made it easier to implement for smaller organizations.
Beyond Device Unlock
Securing access to a device is just the first step. Once the device is unlocked, many apps and services will also have authentication requirements. If you think through the activities that your employees will take on during the day, you might find that they spend a significant amount of time authenticating, typing passwords and probably getting frustrated.
With Samsung Pass, you can use biometrics to eliminate the need for passwords on business applications and web services when using the Samsung Internet Browser. This can make each resource both easier to access for the right user and harder for the wrong ones, as each resource can leverage more complex passwords while also relying on the latest and most secure biometric authentication methods.
Making a Decision
There are many considerations involved in choosing a biometric authentication method, but on a basic level, start with these three:
- What environment will users be in? There are secure options for both looking at and touching the device, with iris scan and ultrasonic fingerprint, respectively, being the most secure. Light, dirt and protective clothing, to name a few, can make one approach or another less workable. With devices like the Galaxy S10 and Galaxy S10+, you can standardize on a device and customize which approach is used by the type of work employees are doing.
- What apps or sites will they use? If users’ work entails multiple sites requiring a login and/or apps with separate authentication methods, consider a unifying password management approach like Samsung Pass.
- Is there a regulatory compliance requirement? If the data being accessed or collected with the device has some implication for privacy, personal information or financial information, consider a multifactor solution. These MFA methods can be very cumbersome unless you can utilize the biometrics built into Samsung devices.
When it comes to biometric authentication, the only choice that is the clear wrong one is to overlook it. The number of data breaches in the U.S. has been increasing rapidly, growing by 54 percent in 2019 alone, with more small businesses being targeted. With so many easily accessible authentication methods available, there’s no reason not to take advantage of them and keep your business and your data safe. With the right method, your mobile workers and data are more secure and, with the help of Samsung’s built-in biometric options, easy to implement and use.
Explore biometric options in greater detail with this infographic, or get a free guide to developing an incident response playbook to help you stop a data breach in its tracks.