With more people than ever working from home (WFH) over the past year, employers have faced a record number of security threats — from online hackers and phishing scams to the physical data breaches that can happen when company devices and data leave the main office. The cybersecurity threats have become more numerous, but they’re not new. Dexter Caffey, founder of Smart Eye Technology, set out on a mission to protect the privacy and security of everyone’s sensitive information three years ago.
The idea for Smart Eye Technology, a platform that secures documents using biometrics, was born at a cybersecurity conference in 2017. As Caffey chatted with another conference attendee (a cybersecurity expert), he glanced at the man’s laptop screen and saw open Word documents and PDF files.
“Why should I be able to see any document on this guy’s laptop?” Caffey wondered. “It’s none of my business!” Then he thought, “What if I could create an app that prevented anyone else from seeing what’s on my screen? An app that would look at their face and say, ‘Nope, I only recognize Dexter’s face. We’re blocking you out.'”
Caffey partnered with a software developer that specializes in biometrics, and in June 2020, he launched the first iteration of the Smart Eye app. Now his company has launched a secure document-sharing platform for small-to-medium-size businesses (SMBs) that includes e-signatures, document activity monitoring and access control features — helping employees be more productive and employers less vulnerable to data breaches.
How it works
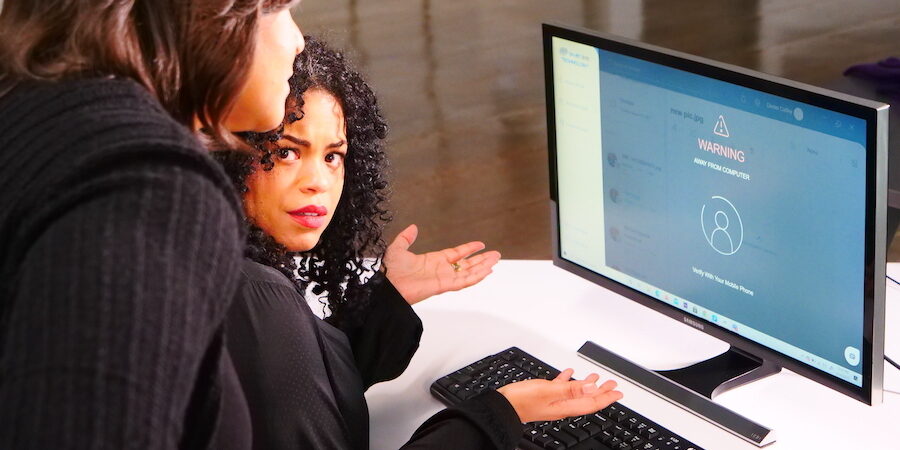
Smart Eye Technology includes a mobile app and a web app, both of which let users upload, share, receive and review files in the platform. When files are uploaded they are secured with a proprietary self-protecting data technology and AES-256 encryption. Users can then share those files with other authorized Smart Eye users who must verify their identity with at least one form of biometric authentication in order to open the file. Facial recognition is always required by the file receiver, but the file sender can request further verification with additional biometric(s) including voice, fingerprint and iris recognition (coming soon).
The sender also gets to decide whether the recipient can download the file or share it with anyone else (the default is set to no for both). And if they accidentally send a document to the wrong person or need to revoke someone’s access, they can terminate access immediately, with the click of a button, even if the document has already been opened by the recipient.
The app continuously scans faces and instantly blocks documents from people who aren’t authorized to access them. So whether people are working from home, in an airport or in any other public place, confidential documents are literally for their eyes only.
For modern businesses, Smart Eye is more than a way to protect documents — it’s also a secure way for teams to collaborate with customers and vendors. System admins decide which companies and individuals can join their “private pond” and communicate with their teams through Smart Eye. Only approved organizations can share files with you in the platform, shutting out everyone else.
Employers can also track and take control of the flow of their data. “Every action on every document is literally documented,” explains Caffey, “so system admins can see who viewed it, who shared it and with whom, who downloaded it or deleted it or signed it.” The control panel (for admins only) provides real-time visibility and transparency over critical business information and all aspects of document access and management, helping companies to proactively identify potential risks and prevent data loss.
Scam-proof business communication
Smart Eye’s private pond helps companies avoid one of the most common cybersecurity threats: phishing emails.
More than 90 percent of data breaches originate from email-based phishing attacks, according to KeepNet Lab’s 2020 Phishing Trends Report. That’s because 1 in 2 people open phishing emails, and 1 in 8 actually share the information that attackers request.
Phishing has been on the rise during the pandemic, and scammers are taking advantage of the widespread shift toward remote work. Caffey has seen businesses fall prey to a number of creative phishing emails, including some that appear to come from the business’s CEO, asking the CFO or bookkeeper to wire money to a fake charity or vendor. In other scams, some phishers pretend to be a regular vendor sending a regular invoice, but with different wiring instructions.
“Smart Eye Technology stops that from ever happening,” says Caffey. “Businesses don’t receive invoices or any other files through our platform unless they have approved the sender.”
Smart Eye is also an identity verified e-signature platform, powered by Adobe Sign. Smart Eye requires biometric authentication to e-sign the document and verifies the signer’s identity. It’s the only security and e-signature solution to do so.
“Many executives have assistants check their email and sign documents for them, but that’s a problem, because now that executive is not responsible for that contract,” explains Caffey. “When you use Adobe Sign through Smart Eye, the document only stays open for the person you sent it to, so you can be assured who signed it.”
Save time by skipping passwords
Not only does Smart Eye “put control and security back into the hands of SMBs,” Caffey says, it also boosts productivity by eliminating passwords, which are easy to forget.
On average, people waste 12.6 minutes per week — or 10.9 hours per year — setting and resetting their passwords, according to Yubico and the Ponemon Institute. That lost worktime costs U.S. businesses $5.2 million a year.
The same report, which included nearly 15,000 respondents, found that 69 percent of people share their passwords with colleagues to access accounts. Another 51 percent reuse their passwords across business and personal accounts — making them vulnerable to hackers — and 57 percent don’t change their password behaviors after they experience a phishing attack.
Bolster your mobile threat defense
Get tips on improving your mobile security, from solution implementation to endpoint management. Download Now
Passwords are easy to hack unless they’re hard to remember, which slows work and annoys employees — 57 percent of whom prefer login methods without passwords. With Smart Eye Technology, letters, numbers and symbols are swapped for biometric authentications which are much harder to hack and impossible to forget.
In the near future, Caffey plans to add another time-saving feature: voice commands that let users verbally send documents and dictate those files’ security measures.
Get smarter about security
Getting started with Smart Eye is as simple as downloading the web and mobile apps, creating a business profile and signing up your employees. Employees then download the apps on their own computers and smart devices, provide their biometrics (which are encrypted to ensure privacy) and start uploading files into the platform.
Smart Eye Technology is an out-of-the-box solution, so deployment is simple, but customer support is at the ready, both via phone and in-app live chat which are available 24 hours a day, 7 days a week.
Caffey’s best tip for success: “Use all available biometric features so you have the highest level of security. Files sent via e-mail can be intercepted, but Smart Eye gives you control over your documents and your data.”
Discover more essential apps to empower your growing business — and explore exclusive business pricing, financing and trade-in options and other deals on everything from phones and tablets to monitors and memory.