As the U.S. government shifts away from its longtime association with previous generations of mobile devices, Android™ is taking an increasing share of the federal market. As sales of Android devices far outpace those of other operating systems (OS) around the world, it should hardly come as a surprise that federal workers in turn are embracing the platform. There remains some reluctance, though, as IT leaders vacillate over the perceived issues within Android security. For example, a recent study from SOTI showed that while two-thirds of global businesses consider Android devices to be integral to daily operations, some 40 percent of those businesses still have concerns over how secure the OS really is.
However, research suggests those fears are unfounded. By most current metrics, the government’s Android adoption is thriving in large measure because of IT executives’ confidence in the OS’ security.
Bring-Your-Own-Device (BYOD) Drives Android Adoption
Government use of Android is due in large measure to the steady rise of BYOD, in which workers are permitted to make use of personal devices in a work setting. Analysts have said the government has much to gain by pursuing this course. The Brookings Institute, for instance, said that BYOD can improve productivity significantly within the $80 billion federal IT budget. In fact, Brookings reports that companies can save up to $3,150 per employee by implementing a comprehensive BYOD solution. Driven by such potential gains, 85 percent of businesses will have a BYOD policy in place by 2020, according to Gartner. Where business leads, government inevitably follows when it comes to IT trends.
Why is BYOD such a strong potential win? Analysts cite a number of reasons. Employees are happier and more productive on devices they already know and like. BYOD can sometimes trim costs, too, by pulling the expense of a device off the agency’s books entirely. Alternatively, the organization can share costs with the user. Personnel devices also tend to be ahead of the tech curve compared to those acquired on a government purchase order. That means BYOD can make workers more efficient.
Safe Apps Mean Safe Devices
Despite promised returns, some government agencies have been slow to establish BYOD or to allow the Android OS into their stable of devices. This is largely out of long-held concerns about security weaknesses. Yet, a growing body of evidence suggests that Android security is just as strong as, if not stronger than, that of other operating systems. One telling figure comes from Google’s Android Security 2014 Year in Review. Having reviewed extensive usage reports, Google concluded that less than 1 percent of Android devices have any malware at all.
When things do go wrong, the problem typically can be traced to apps downloaded from someplace other than the official Google Play Store. While unofficial sources may offer a range of apps, they typically lack the vetting process needed to ensure security. An unregulated store may thus be a playground for malware producers. To help safeguard Play Store users, Android deploys Verify Apps, a program that watches for apps downloaded outside Google’s shopping environment. In addition to alerting the user to new apps, Verify Apps performs continuous monitoring to ensure an added level of protection. This ability to monitor apps is continuously a fundamental component of mobile security. Apps are among the most vulnerable aspects of the mobile security landscape, moving targets that require constant attention.
Google is constantly seeking out potentially harmful applications, Android lead security engineer Adrian Ludwig said at the recent RSA Conference 2015. “We break that down, region by region, and by types of apps,” he said. “The traditional PC model of thinking about malware is that all malware is kind of the same: It can compromise your device at a holistic level. In Android, because of sandboxing, for a developer who wants to protect e-mail, we see maybe 10 to 20 out of every million installs of something that would go after that data. You compare that to how many devices are lost every day or stolen, and you start to realize that this is the real threat: physical-world threats.” This ability to monitor apps is a significant feature driving Android security. In CIO Magazine, Mark Hammond, senior manager for Cisco Security Solutions, said the threat of Android malware is “directly associated with the source. If the average user is sticking with a well-regulated app store, like Google Play, then the risk of malware diminishes significantly.”
Containerization Safeguards Work Data and Personal Usage
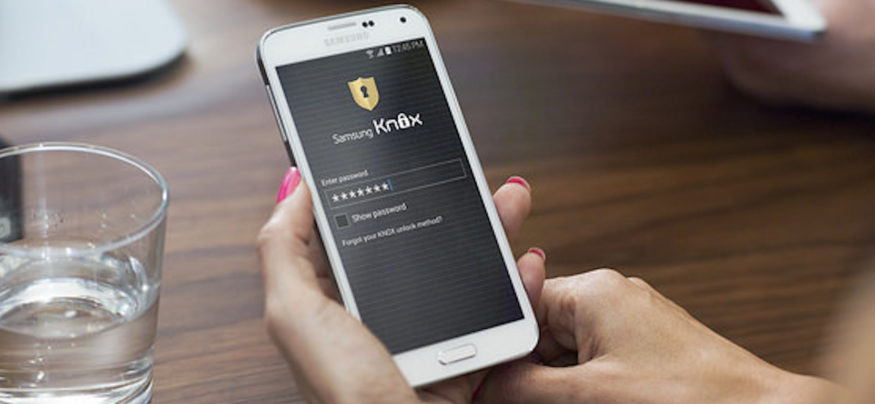
For federal IT managers who worry that their users will ignore such warnings, there is Samsung KNOX, a containerization solution designed to create a virtual partition on Samsung portfolio of Android devices, segregating work data from personal materials. In effect, KNOX, which is built into the Galaxy S® 7 and Galaxy Tab® devices, creates a new layer to securely separate personal and professional activities on a device. Password protection ensures that work materials can’t be accessed, and the solution limits the ways in which work data can be used.
KNOX has sparked interest among federal IT planners. For example, the FBI and the Defense Information Systems Agency have begun implementing KNOX within their own capabilities. By satisfying BYOD demands and distinguishing work from personal use, KNOX goes a long way toward ensuring ongoing Android security.