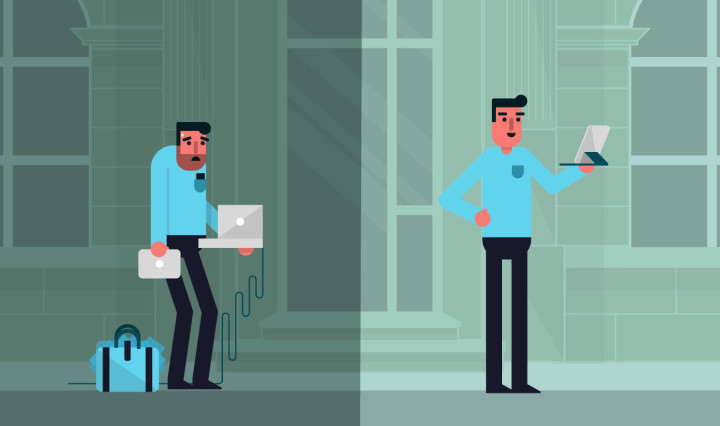
A popular catchphrase, “enterprise readiness,” is used to describe a device that can hit the ground running in terms of usability and functionality. But there’s another side to readiness — security. For IT managers sizing up a new 2-in-1 or notebook for their enterprise workforce, it’s worth understanding the security features baked into Windows 10 Pro, as well as some of the additional security features available within Windows 10 Enterprise, an upgrade from Windows 10 Pro through your volume licensing agreement.
Ready, Set…
First, what is readiness? In its typical usage (setting aside the security aspects for now), enterprise readiness refers to a device complete with a robust operating system and appropriate applications, one that can serve the needs of an enterprise out of the box.
These needs may cover a range of functions. Readiness at the device level may include the availability of core productivity apps like Office, seamless integration with leading software platforms or access to business-focused mobile applications.
Assuming these fundamentals are in place, an enterprise must then turn its attention to security considerations.
New Level of Protection
Windows 10 security delivers an unprecedented level of protection for mobile information across the enterprise, defending such basic functions as email, docs and apps. Windows 10 Pro gives the enterprise command over mobile device management and mobile app management, while Windows 10 Enterprise adds additional safeguards on top of those available in Windows 10 Pro.
First let’s take a look at Windows 10 Pro, whose basic protections will keep all private corporate data encrypted, contained and under IT control. Managers will be able to detect and prevent tampering, security threats and vulnerabilities before they’re exploited by bad actors, while centrally managing policy and security configurations across all mobile devices.
Are your mobile workers ready for a 2-in-1 laptop?
Here are five indicators that your employees could benefit from a 2-in-1 device. Download Now
Drilling down to specifics, Windows 10 Pro security measures include:
- Enterprise Data Protection, which makes it easier to perform data separation and containment of corporate data. With the use of containers, this feature protects data wherever it exists on the device.
- Through its Trusted Boot feature, Windows 10 Pro closes off the pathways that allow malware to hide from the OS on startup. Hardware-based virtualization isolates key processes from the system so they cannot be tampered with.
- Conditional access, achieved through the Windows Device Health Attestation cloud service used in concert with management systems such as Microsoft Intune, helps prevent untrustworthy devices from gaining access to corporate resources.
- New access controls also are delivered via Microsoft Passport, which replaces passwords with an easy to deploy two-factor password alternative that is accessible by using a PIN or Windows Hello. This means enterprise-grade security can now support fingerprint, facial and iris-based recognition.
- Windows BitLocker Drive Encryption provides better data protection for your computer by encrypting all data stored on the Windows operating system volume. BitLocker uses the Trusted Platform Module (TPM) — a microchip built into a computer — to help protect the Windows operating system and user data, and helps to ensure that a computer isn’t tampered with, even if it’s left unattended, lost or stolen.
- Device Encryption “scrambles” data to help keep it secure. Only someone with the right encryption key (like a password) can unscramble and read it. Device encryption helps block hackers from getting the files they need to steal your password. If your PC itself is lost or stolen, device encryption also helps keep other people from accessing your data by physically installing your locked drive in a different PC.
- In line with this theme of simplicity and security, Windows Hello delivers an elegant answer to the common problem of too many passwords. By granting access based on a fingerprint or a face, Windows Hello makes access both streamlined and secure. Moving forward, free updates will help people stay current for the supported lifetime of the device.
- Another arrow in the security quiver, the all-new Microsoft Edge browser has been designed to be the most secure browser ever released by Microsoft, using advanced sandboxing technology to isolate users’ personal information from their online experiences.
Stronger Still
For those seeking additional layers of protection, Windows 10 Enterprise offers a pair of complimentary features meant to deliver heightened safeguards. Together, Credential Guard and Device Guard bring security to an enterprise-grade level.
Device Guard is actually a group of key features that work together to harden a computer system against malware. The focus here is on preventing malicious code from running by ensuring that only known “good” code can execute.
A separate feature, Credential Guard aims to isolate and harden key system and user secrets against compromise, thus helping to minimize the impact and breadth of an attack in the event that malicious code is already running via a local or network-based vector.
The two complement each other, offering different protections against a range of threat types.
Whether one pursues Windows 10 Pro, or opts for the added security features of Windows 10 Enterprise, it’s clear that there is power to spare in the broad range of protections integrated into the latest generation of Windows.
Learn more about how the latest Samsung mobile devices can boost productivity in the enterprise.