Warnings about phishing attacks are ubiquitous in enterprise cybersecurity awareness programs. Posters line government agency hallways warning users not to click strange links. Security teams include stories in agency newsletters warning of the risks associated with email messages from unknown senders. But unfortunately, experience consistently shows that these warnings simply aren’t effective enough, and that users will still click on links in phishing attack messages out of curiosity, ignorance or simple naiveté.
But what does it mean for companies with scaling mobile environments that are transforming the way workflows are created, managed and executed?
In Verizon’s annual “2020 Data Breach Investigations Report,” released earlier this year, it’s clear that phishing attacks aren’t slowing down — in fact, they’re gaining traction — and that could spell trouble for enterprises focusing on a mobile-first or mobile-only environment.
What is phishing?
Put simply, phishing is the use of email messages to gain user trust, ultimately giving the perpetrator an actionable item, either by clicking on a link that will in turn take them to a malicious site, sharing sensitive information such as passwords or credit card information or even installing malware on the device being used.
According to Verizon’s report, email was still the top entry point for malware, accounting for about 90 percent of known attacks. Because mobile employees receive emails to their smartphones or tablets, this puts devices accessing company data at risk — regardless of your company’s mobile deployment strategy.
Phishing attacks pose danger to the entire company
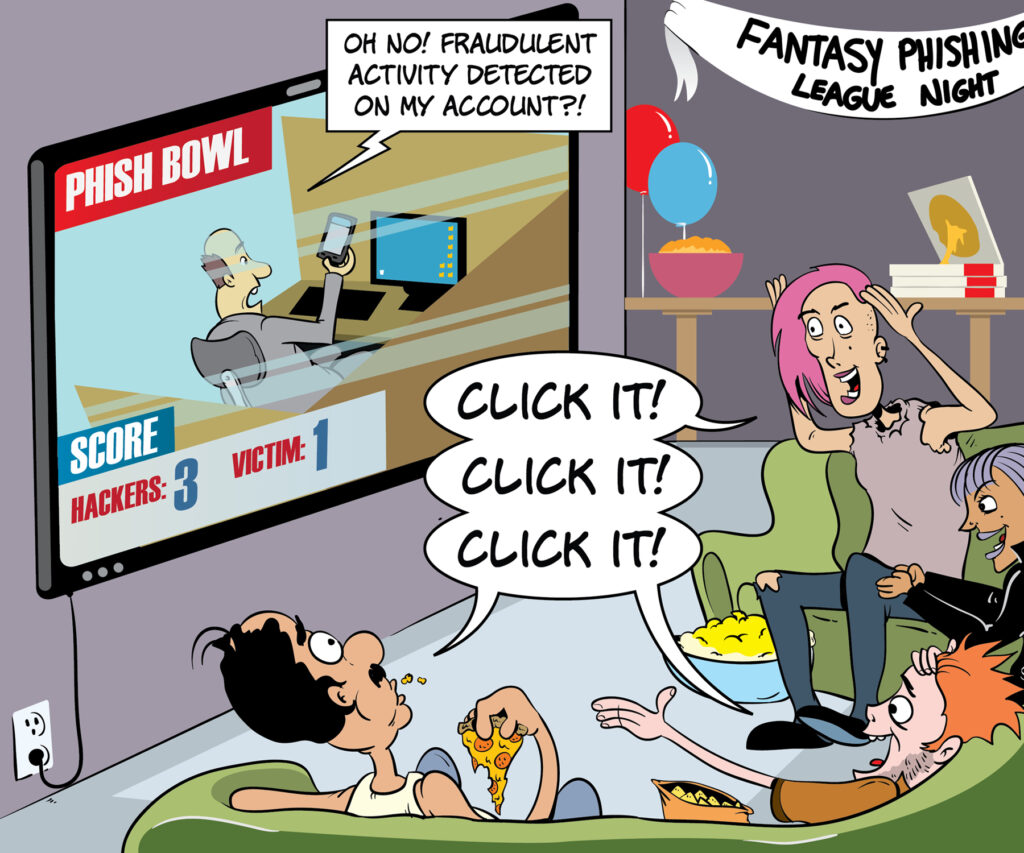
Enterprise security teams have much to learn from this study. First, the security risk posed by phishing attacks is significant. One individual clicking a malicious link can single-handedly jeopardize the security of the entire organization. The results of this study show that the likelihood of a well-crafted message successfully generating clicks is very high. Users must understand the dangers posed by phishing and view every message they receive with caution. They must also understand that visiting malicious sites endangers the entire organization and may violate corporate security policy.
Tests reported by KnowBe4 for the “Phishing By Industry 2020 Benchmarking Report” indicate that 37.9 percent of employees across all industries were likely to click on a suspicious link or email or obey a fraudulent request. Within 90 days after awareness training, the percentage of those phishing-prone employees dropped to 14.1 percent. Unfortunately, it only takes one person to open the floodgates via link.
Malware matures on mobile
There’s a clear juxtaposition, however, when it comes to the difference between desktop and mobile phishing scams. According to a 2018 report from Lookout, mobile phishing attacks increased 85 percent every year between 2011 and 2016. Additionally, 56 percent of users tapped on a phishing URL via their mobile device.
So why the skyrocketing penetration attempts on mobile, compared to the slowing attacks for ordinary usage? Because mobile devices — smartphones, tablets, wearables — are exactly that: mobile. Sitting inside the company headquarters attached to a secure Wi-Fi connection enables security protocols to work at their zenith. The moment that a mobile device’s user walks away and begins tapping into foreign connections — pineapples posing as hotel Wi-Fi, inadvertent hot spot connections, etc. — many mobile security features begin to fail.
The beginner's guide to mobile device management
Learn how to use MDM to your small business' advantage with this comprehensive guide. Download Now
That’s why a security protocol with baked-in, layered components that will protect the device regardless of connection is the first step in throwing those phish back into the water from which they came.
Samsung Knox provides a multilayered approach to mobile device security.
Built into Samsung’s smartphones and tablets, Knox is a defense-grade security platform that protects your device from the moment you power up — so you can focus on what matters to you and your business. Knox defends your device against intrusion, malware and malicious threats. The most sensitive data on your device is secured by Knox, including your biometrics, passwords, personal data and other credentials. Advanced runtime protections block any unauthorized access to your phone’s kernel, in real time.
For IT departments, Knox also provides a full set of cloud-based management tools to optimize security across a device fleet. The Knox Suite combines Knox Mobile Enrollment, the Knox Manage enterprise mobility management (EMM) solution, Knox Platform for Enterprise and Knox E-FOTA for operating system (OS) update management. These tools provide a full range of options for enterprises, including integration with advanced virtual private network (VPN) and threat defense platforms.
For individuals, Samsung Galaxy smartphones allow you to create a Secure Folder to keep your personal content private and protected. You can also take advantage of Samsung Pass to conveniently access accounts and apps with just your fingerprint.
Even if a user clicks a malicious link, the attacker won’t be able to penetrate the secure zone and gain access to sensitive information. This multilayered approach helps to mitigate the risk of phishing attacks, in spite of employees’ almost uncontrollable urge to click those links.
Learn how to keep your business data secure across your mobile device deployment in this free beginner’s guide to MDM. Then discover how Samsung Knox is setting a high bar for the most secure phone.