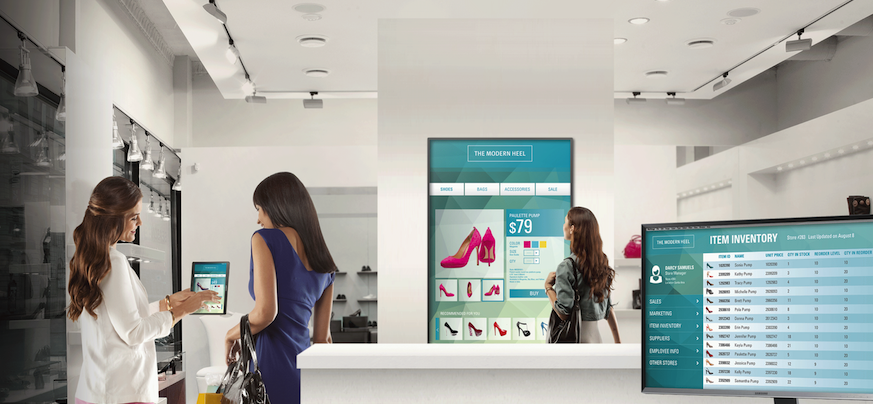
Mobile devices have become a critical part of retail operations, for both back-office and on-the-floor applications. With their flexibility and intuitive touch-screen interfaces, associates and managers are using smartphones and tablets for inventory management, clienteling and mobile point of sale (mPOS), as well as other specialized use cases.
Although early mobility projects used custom devices and operating systems, this has changed over the past five years as the ecosystem around Android smartphones allowed reduced costs and faster deployment times. However, using commercial off-the-shelf mobile devices means that IT administrators need to implement additional security measures to customize devices for their retail use case.
Configuring tablets and phones for retail environments is simple: work with the device, set up the network and tailor any back-end applications.
Device Security
Devices in a retail environment should be kept under fairly strict control, typically using mobile device management (MDM) or enterprise mobility management (EMM) software. Because these devices are dedicated to specific functions, IT managers should use MDM or EMM to lock devices down.
For example, application store access should be restricted to approved sources, whitelisted applications and established network profiles, so that only authorized wireless networks are used. For Samsung tablets and smartphones, Knox Configure provides additional, more granular customization capabilities that allow admins to pre-configure device settings, disable bloatware and even remap physical buttons.
Device authentication also brings two main considerations. First, since retail devices are often shared, a standard smartphone operating system designed for a single user means common passwords to unlock the device. This puts the onus on the retail application to re-authenticate the true user of the device. Organizations and IT should consider what authentication methods would offer the best level of security without needing to share passwords among staff.
Prevent a Data Breach in Your Store
Download this guide to increase information security in your store's digital and mobile environment. Download Now
Second, retail applications may require additional specialized hardware, such as a barcode, RFID or credit card readers, and an outer case that may block authentication tools. IT managers will want to bring these issues up with application developers early to ensure that security isn’t dropped. Smartphones with newer authentication systems, such as iris scanners, may be worth investigating if they can be linked to the back-end application.
The retail environment is also one where device loss and theft is a significant security issue, so IT managers should ensure that all devices have a bare minimum of corporate data on them, and certainly no customer data. This helps to mitigate the data loss risks and liabilities if a device goes missing.
Network Security
The next step is to set up the devices within proper networks. Although stores don’t use unsecured Wi-Fi networks for retail applications, the network should be secured with WPA2-Enterprise to eliminate shared passwords and ensure data encryption.
Since devices are shared, device authentication — rather than user authentication — should be in place to gain network access. Of course, devices must also have a very limited set of networks and certificates they trust, managed by MDM or EMM tools. Smartphones or tablets that store keys and digital certificates in a Trusted Execution Environment (TEE) are the best choice to reduce the likelihood of network break-in, because the network authentication information can’t be extracted even if the device is lost or stolen.
However, even with WPA2-Enterprise on the network, device applications should assume the network is insecure, because the backhaul from the wireless network to the backend server is an easy vulnerability for someone with physical store access — not to mention the future potential security issues in WPA2 that might show up.
Thus, applications should use industry-tested security tools such as properly configured TLS/SSL encryption, with digital certificates for authentication, for all over-the-air data. IT managers should examine the TLS configuration within applications, because the recommendations for encryption and data integrity algorithms are constantly being updated, and old versions of the TLS protocol suite may be configured to allow algorithms that are no longer considered secure.
Application Back-End Security
For retail applications, the ultimate security nightmare is the loss of customer financial or personal identifying information (PII). On the financial side, the PCI Data Security Standard (DSS) must be followed to maintain regulatory compliance and implement best practices. Newer PCI standards, such as the Payment Application DSS (PA-DSS) and PIN Transaction Security (PTS), should also be considered during development.
However, PCI’s requirements should be considered minimums, not a comprehensive program. Application developers and vendors should be using application security best practices, such as avoiding the OWASP Top 10, even when applications are not Internet-connected.
Applications and networks need to minimize the storage of customer financial and PII data — on the device or in the cloud. One approach is to use compliance-audited service providers and off-the-shelf applications, as these approaches reduce overall risk and liability. IT departments can also evaluate data separation solutions, which set up secure environments to store data and are accessible through specific authentication methods.
Keeping Retail Technology Up-to-Date
For long-term maintenance, IT managers should consider scheduling penetration testing or red-team testing as applications are rolled out. Although the focus should be on the back-end applications, testing should consider the entire retail chain to help identify any weaknesses that need revisiting or fine-tuning.
By enacting these practices, retail environments can ensure their defenses and devices evolve as new security threats emerge.
Are unpatched security vulnerabilities worth the risk? A recent report shows just how much known vulnerabilities can cost your business.