In this News Insight, Ars Technica discusses the need to balance data accessibility for employees with a stringent security system that will prevent corporate data breaches. You can take this short quiz to determine if you have the right mobile security plan for your business. —Samsung Insights editorial team
The c-suite and managers are often on the move while making critical decisions. They need to understand what’s at stake. They need to see the numbers, hear the sensitive details of a situation. And usually, they haven’t incorporated the latest guidelines from their security team.
Karen Scarfone of Scarfone Cybersecurity expects security for executives to be particularly stringent. “They have access to so much highly sensitive data and the authority to do things that others don’t,” she says. “Plus, they’re highly likely to be targeted.”
2016 was a banner year for database breaches. The Identity Theft Resource Center reports that American companies and government agencies allowed 1,093 breaches of their data. That record total equates to a 40 percent increase from 2015. And those are just what organizations reported.
Most everyone at a company accesses data remotely. Often they’re handling integral company information and—to the chagrin of IT—they’re not always following the most secure rules. But few check those boxes more firmly than high-powered decision makers.
“We give executives far too much privilege to sensitive systems,” says Brand Barney, an analyst at SecurityMetrics. “More often than not, they don’t need that access.”
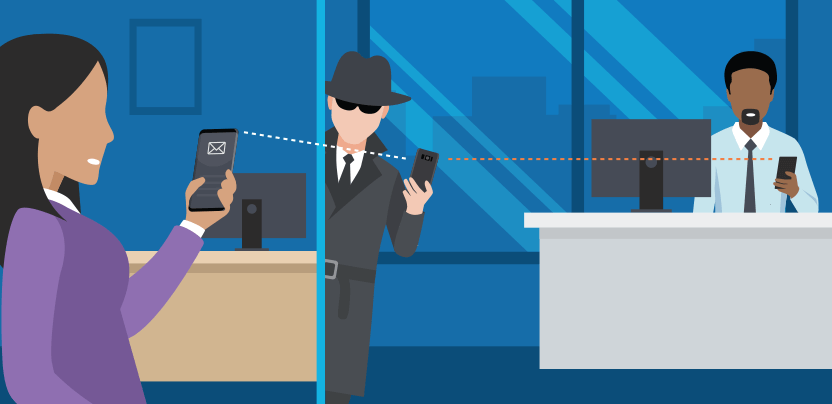
Executives are only part of the equation, however. As devices move farther from central IT’s control—in both physical distance and the number of systems required to re-access work—they inherently create weakening behaviors. They download applications (that may contain malware), leave a device unattended at a bar or commit any of the infinite other possible behaviors that make people with devices unpredictable. So as businesses integrate with each other—exchanging digital products, documents, and payment logistics across the Internet—they bring even more people into the equation and open up further remote weak points.
This sometimes causes companies to suffer that aren’t directly responsible for allowing the attacker in the first place. In late April, a hacker (or group) called thedarkoverlord leaked new episodes of Netflix’s Orange Is The New Black online after claiming the company refused to pay a ransom. Later, The New York Times reported Larson Studios, a post-production audio vendor, was the source of the breach—though the exact method of the attack is still unknown.
And everyone, despite hacks being a weekly feature on the news, still violates the most basic security practices. Bomgar, a security firm that secures company’s remote access points, reports a litany of statistics that show how employees leave the door open: Over two-thirds of remote access employees don’t log out when they’re done. About half write down their passwords, send work files to personal email accounts, or login from unsecured Wi-Fi networks.
Why You Need Samsung Knox on Your Work Phone
Learn why Knox remains the top security platform for work phones. Download Now
Of course there are plenty of ways in besides tracking executives and third parties. Sam Elliott, director of security product management at Bomgar, believes, “It’s a lot easier for a threat actor to do a quick search on the Internet and find an unsecured remote access pathway into an organization than it is for them to use more mature tradecraft like phishing or some brute force access.”
Even when a company goes public about a breach (usually required by law), they restrict details. “What we don’t see is how companies are breached internally,” says Barney, because solutions can be expensive and companies don’t want public finger pointing. But without that accountability, Barney says companies aren’t motivated to completely patch holes and often remain vulnerable even after the headlines have passed.
Barney argues too many organizations still build “flat networks,” meaning if an attacker gets access to one area, like sales metrics, they get to everything else, like customer information. One of the most effective security measures for remote access is also the hardest to implement: two-factor authentication. Requiring an attacker to compromise two different devices to gain access creates an exponentially more difficult barrier—but also complicates IT’s job.
Today, most companies use virtual private networks (VPNs) to connect remote employees to sensitive data. But those credentials can still find their way into an attacker’s hands. Dennis Griffin, product manager at cybersecurity firm Vidder, warns of leaning too heavily on VPN for security. He notes that recently more than half a billion usernames and passwords were being sold on the Dark Web.
“They came from previously reported breaches of LinkedIn (117 million credentials) and MySpace (427 million credentials),” he says. “It’s very possible that your contractor, vendor, or service provider uses the same credentials for your remote access VPN as for his social media account.”
For now, attackers seem set on re-proving the old adage that security’s only as strong as the weakest link. Remote weak points will continue giving security managers fits.
“How many IT managers are willing and able to implement and enforce stringent requirements on senior management?” Scarfone asks. “Especially with the widespread perception that security hampers productivity?”
And that’s the balance that shows no sign of going away. A network can’t grow without developing holes—and as long as there’s revenue involved, someone else will always want to take a peek. If big organizations want decision makers to have power, they’ll need to keep the most powerful security chips underpinning their devices, where security’s in place from the web browser down to the root hardware.
Discover if you have the right mobile security plan for your business by filling out this assessment.