In this News Insight, WIRED Magazine discusses how to prepare for mobile security threats — and what to do if you lose your phone. If you’re ready to strengthen your mobile security, download our free ten-step guide to keeping mobile data safe. — Samsung Insights editorial team
The ubiquitous mobile phone is a convenient and essential part of your personal and business lives. But is it secure if it’s lost or stolen? Not likely.
Here’s another twist: Even if you’ve got the phone in your hand, it may not be safe. One in five organizations experience a mobile security breach without a device being lost, primarily the result of malware downloaded via very hackable public Wi-Fi connections. If you’re on a company phone and pull in ransomware, you could be endangering the future of your company. More than half of small companies hit by a significant cyberattack fold within six months. Some security firms report that public companies often suffer a significant drop in their stock price the day a breach is announced, and lose long-term customers.
The benefit of open systems on the job is undeniably huge. Mobile helps industries worldwide work smarter and faster by providing anywhere, anytime data access to employees. But mobile security threats are soaring, and everyone needs a security plan. That starts with two things: “education and awareness,” says Jonathan Wong, director of product marketing at Samsung. “Mitigating your exposure to risk is one of the most important things you can do.”
Secure Your Phone with Intelligent Scan
Learn how Intelligent Scan enables simple and secure device unlocking in this infographic. Download Now
Wong cites three major areas of concern: physical exposure (if a device is lost, stolen, or tampered with); malware, which penetrates the device and gets to the root code; and data in transit, after it leaves your phone and is on a cellular or Wi-Fi network.
By preparing proactively for mobile security threats, you can make your phone a lot more secure with a few easy steps. Here’s how.
First, Lock It Down
- Build a wall. Some mobile phones allow their users to put a firewall between work and personal data, an attribute called containerization. Typically this happens when your employer lets you keep personal data and apps on your company phone. In one section, you’ll have a secure work container that holds a report from the CFO. In another, photos of your kids in the pool. The two data containers do not intermingle. If your phone is mislaid, for instance, corporate IT can remotely wipe sensitive data as a safeguard, while leaving your personal data untouched. Samsung’s smartphones offer the Knox Workspace and Secure Folder, which separates corporate data and applications from personal information and apps. For example, add your personal banking app to Secure Folder and if you have Iris/fingerprint identification turned on, your bank account access is now protected by biometrics on your mobile phone.
- Shuffle your password deck. Traditional passcodes don’t cut it anymore. They’re easily cracked, and many people use the same one for multiple accounts and applications. Steal it and you have them all. Newer mobile phones are now starting to offer built-in password managers. These will enable you to create and manage unique passwords for every website you visit.
- Go for unique identifiers. Biometric authentication offers an even more secure approach. The fingerprint scanner has been on high-end smartphones for several years. More recently, facial recognition is a fast and convenient way to unlock your device—although not as securely as other biometrics, such as fingerprints. The next step up is iris scanning. It’s the most secure, but rare so far.
- Back it up. Your phone is just a physical vessel. It’s the material on it that matters. So back it up regularly. Mark a specific time—say, Friday at 5 pm—when you’re going to do it. Most phone carriers, manufacturers, and operating systems offer free wireless backups to their cloud.
- Tag it. Seems simple, but it’s effective. Pop a business card or slip of paper with contact info between the back of the phone and the protective cover. If someone finds it, they may find you.
Dude, Where’s My Phone?
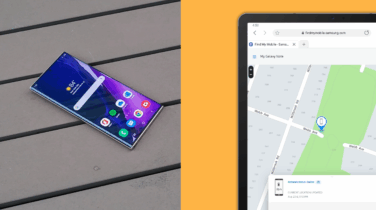
- Activate your “find my mobile” feature. It’s an essential remote-location tracking feature, enabled by ubiquitous wireless connectivity and GPS satellite data. If your device is stolen, you can attempt to track it down or prevent its reactivation. You may have mislaid it, if you’re lucky. But you’ll have a sense of where it is.
- Move fast. If your phone is irretrievably gone, log on to every account you had on your phone and change your password. Start with any accounts where you use a credit card, such as retail locations or your bank. Do the same with email and social network accounts. Inform your financial companies and manager (if it’s a work device) that you’ve lost your phone to alert them to possible fraudulent charges or activities.
- Wipe it. If your mobile is truly gone, you’ve got no choice: Remotely wipe it, removing all of your personal data. If the thief did manage to gain access to your lost or stolen device, they’d find no important personal information.
If You Get Your Phone Back
- Wipe it anyway. Some nasty person may have put spyware or a malicious app on it while it was out of your hands. So first check the backups on your computer or cloud service to make sure that you have copies of the really important things, then revert it to factory settings.
Every phone is vulnerable. But with a few quick steps, you’ll make it a lot harder to crack.
This content is produced by WIRED Brand Lab in collaboration with Samsung.
Get your free guide to better securing the personal and work data on your mobile phone.