In today’s digitally transformed enterprise, mobile devices have become essential business tools, capable of supporting virtually every worker in their daily tasks. However, without effective mobile device management (MDM), IT leaders struggle to optimize smartphones and tablets to serve diverse business roles efficiently.
To maximize productivity and ensure security, administrators need greater control over how devices operate, which apps are installed, and the networks they connect to. Samsung’s Knox Configure gives them that control and enables them to manage and optimize smartphones and tablets.
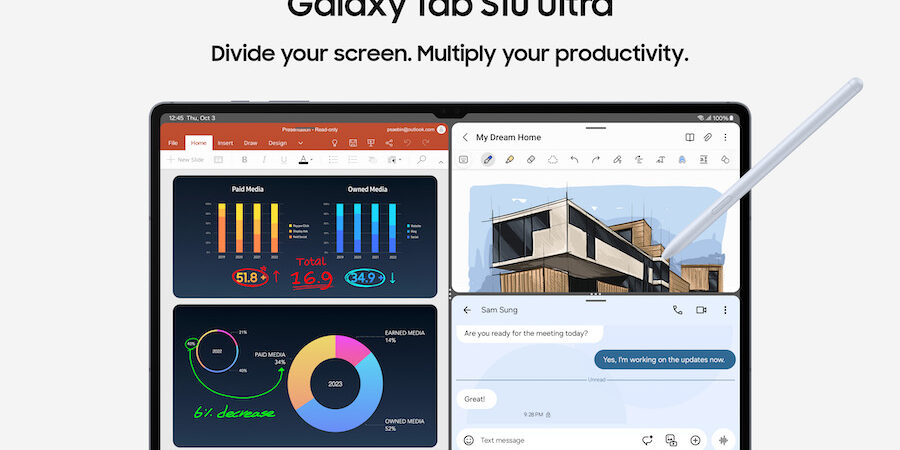
Granular device configurations allow your IT team to ensure that corporate-liable devices like Galaxy Tab S10+ and S10 Ultra won’t leak information or expose the company to security vulnerabilities. Whether deploying a few dozen devices or a few thousand, Knox Configure can make the job easier.
What exactly does device configuration mean? With Knox Configure, you can control and customize almost every aspect of the device, even without unboxing.
Seamless, out-of-the-box setup with Knox Configure
Knox Configure goes beyond traditional MDM solutions by giving you full control over the features your employees can and can’t access on their corporate-liable devices. You can set up each device according to the employee’s company role or security clearance. You can also provision content and apps, disable other preloaded apps employees don’t need and rebrand your devices with a custom boot animation.
Knox Configure allows the mobility manager to create a gold master image that’s automatically applied to all end users’ devices. In the Knox Configure portal, admins can upload a list of deployed devices and assign them predefined profiles, tailoring the devices to various business needs. Rather than going through setup wizards or other complicated steps, employees’ mobile devices are automatically provisioned and configured as soon as they’re powered on and connected to a network. And IT managers don’t have to sink time into manually configuring each device. This can also be done after a device needs to go through a factory reset.
Gain advanced device provisioning
One of the most important settings on any mobile device is how it connects to the world. Connectivity is necessary for improving employees’ productivity, and there’s rarely a reason to disable this access for standard usage. However, if employees are accessing highly sensitive information, you may have to limit connectivity to ensure data security.
By using Knox Configure, you can control Wi-Fi, LTE and 5G connectivity, and even set up mobile network Access Point Name (APN) configurations. You can turn off GPS, Bluetooth and near-field communication (NFC) or enable Flight Mode. These are especially vital controls for specialist industry use cases or employees handling sensitive data.
However you configure your devices, Knox Configure prevents your employees from reversing these settings, even with a factory reset. You maintain stronger control over how data flows in and out of your network — and, more importantly, who can access it.
Building on these capabilities, the Knox Configure Dynamic edition makes it easy to keep corporate-liable devices on the latest settings so they’re always up to date.
Create purpose-built mobile appliances
Almost every feature on your mobile devices can be customized with Knox Configure according to your unique business needs. You can help minimize employee interference with device settings or eliminate interference for customer-facing devices. By setting up a Galaxy Tab S10+ or S10 Ultra device as a self-serve kiosk, for example, you can provide wayfinding information for hotel guests or have visitors check in when they arrive at an office. You can further customize the UX by modifying the standard UX and locking down the device to a single app, transforming mobile devices into tailor-made business tools.
You also limit potential security vulnerabilities by preventing certain features from being tampered with. If a configured device is lost or stolen, you can reset the device remotely and prevent data leaks by disallowing files from being copied to an SD card or USB storage.
What's the best phone for your business?
Discover the smartphone most tailored to your business needs. Download Now
For devices used in highly sensitive areas, you can use Knox Configure to disable the microphone, camera, or screen capture and limit recording capability. You can also limit communication by locking SMS and MMS message access.
Brand your configured devices
The employee experience can make all the difference in improving your business performance. You can add a personal touch to their mobile devices by using Knox Configure to create a fully company-branded experience from the moment an employee powers on their device.
You can further personalize their devices by preinstalling specific business apps over the air or adding shortcuts, like an icon that goes straight to the company’s homepage. For customer-facing devices, a shortcut to customer support can help ensure a smooth transaction.
Offer flexibility for multiple users
For businesses managing shared devices, MDM becomes even more critical. When multiple people use enterprise smartphones and tablets, IT usually faces a number of issues around device configuration. But with Knox Shared Device, IT can let multiple users access the same device without sharing data. Individual settings, accounts, apps and policies are exclusively applied to a single user account. Data doesn’t pass between accounts and is cleared when a user logs out. Each user logs into the device with a separate account (with their Active Directory credentials) and only manages their files and apps.
Knox Configure for any industry
Mobile devices have become ubiquitous and increasingly diverse, but they don’t have to be hard to manage. Knox Configure offers dynamic capabilities to meet your unique business needs, whether you pair it with a mobile device management solution or not. With Knox Configure, you can enjoy the benefits of standardized, consistent and secure mobile devices — and plenty of room to innovate.
Pairing an MDM solution with Knox Configure can extend your management capabilities. Find out why your business should deploy MDM solutions. One such solution, Knox Manage, allows your IT team to manage devices from an intuitive cloud-based console.