When smartphones first started gaining popularity over a decade ago, they quickly became the targets for theft because of their inherent value as expensive electronics. By 2013, 3.1 million Americans were reporting a smartphone stolen annually, doubling the previous year’s record.
As noted by many journalists at the time, by weight, smartphones are far more valuable than solid silver. As the way we use mobile devices has changed, the relative value of the hardware itself versus the information stored on the devices has shifted — but both threats continue to be taken very seriously. In the U.S., the Federal Communications Commission (FCC) still produces an annual guide for consumers on how to protect smartphones and deal with their disappearance.
However, there are several simple steps you can take to make losing your smartphone less costly and improve your chances of getting it back.
An ounce of precaution is worth a pound of cure
All mobile security practices are greatly enhanced if you take a few precautionary steps when you set up your new phone.
- Set your lock screen: The single most important thing every smartphone user should do to protect their information, make their phone less valuable to thieves and avoid identity theft is set a lock screen on the device. Not using a lock screen is like leaving your house with the front door and windows wide open. For greater security, use a passcode or PIN with at least six digits. The newest devices also include biometric authentication features like face recognition and fingerprint scanners to make it easier for you to get into your device, while keeping others out.
- Back everything up: Most smartphones today include apps and services for automatically backing up your content and contacts. Make certain you have these cloud backup features turned on and that you understand how to retrieve the information. If you know that everything can be recovered, you won’t hesitate to wipe the device clean if it’s lost or stolen.
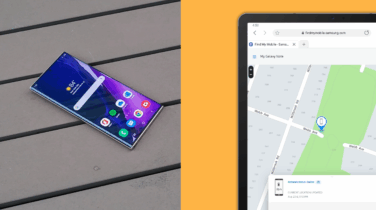
- Make it easier to find: Understand and utilize the built-in device-finding features, such as Samsung Find My Mobile. Most devices can be located on a map using GPS or with a loud sound emitted from the phone. Some will also allow you to lock the device and display a message and contact phone number on the screen.
What to do when disaster strikes
Major smartphone operating systems, along with practices by governments and mobile carriers, have provided all smartphone users with a set of tools and remediation that make smartphone theft less attractive, and provide means of ensuring a device gone missing is less tragic.
- Do not wait: If you realize that you don’t know where your device is, and you are anywhere but in the comfort of your home, take immediate action. If it is stolen, every minute you wait increases your chances of not retrieving the device, losing information and having your identity stolen. If someone is able to disable the ability of your device to communicate with the internet, all hope of retrieval and additional protections are likely lost.
- Try to find it: Use the device location services presented above to attempt to find your device. These tools can help not only to locate your device, but also give you a quick answer on whether your device is in a retrievable place and condition. If you are not able to locate it almost immediately, move to the next step.
- When in doubt, treat it like a crime: Most of the same tools used to attempt to find your device will give you the ability to put it in a mode for lost or stolen devices, including locking the device and if needed removing all the information stored on it. If you’ve followed the precautions above, everything important on your device is already backed up to a safe, cloud storage service — even if you are not certain how to retrieve it yet. Samsung Find My Mobile gives you some additional tools: you can prevent the device from being powered off, have a contact message appear on the screen and put it in power-saving mode to extend the window of opportunity you’ll have to locate it. As a last resort, you can wipe all information from your device so it cannot be used to steal your identity.
- Report it to your carrier: Your mobile service provider can take measures on your behalf to help locate your device and suspend service. Devices that connect to a cellular network contain a small chip called a SIM card that allows the device to communicate over the network. A stolen SIM card can allow someone to place calls and consume data, and you will be liable for those costs. The FCC’s mobile protection guide includes a list of contact information and procedures for major providers in the U.S. if you need to contact your carrier.
Even more tools for businesses of all sizes
All of the risks are even greater for business users and their employers. Many users do not have clear boundaries between their personal and business information on their devices, taking them to places they would never take other business assets. Statistics on lost and stolen devices show these incidents are relatively equally divided between business and nonbusiness hours, and that, while restaurants are the most likely offenders, your phone is as likely to be stolen at work as at a nightclub.
All modern smartphones have built-in application programming interfaces (APIs) that make it possible even for small and medium-sized businesses (SMBs) to institute additional security measures, again increasing the likelihood of retrieving a lost device. Mobile device management (MDM) software places a small program, or agent, on a mobile device that allows an IT admin to enforce policies on the device. These policies include requiring employees to use a secure passcode, preventing the download of risky apps, and controlling other aspects of the device, including locking and wiping devices when lost or stolen. For a business, this provides a layer of consistency across all the devices that are accessing your corporate data. The benefits of being able to manage and control a set of devices in a consistent manner make it well worthwhile to consider owning all of the devices used in your business.
Mobile device management for beginners
Get started with MDM so your organization can spend less and do more — securely and efficiently. Download Now
Once you have installed the MDM agent on the devices, the management console lets you set each device to meet a set of minimum security requirements, as well as enable a consistent experience. If properly configured, you can make mobile work both more easily and more securely at the same time.
Samsung mobile devices come with a long list of enterprise security features that have helped them gain approval for use by government, law enforcement and defense agencies around the world. The Samsung Knox platform, which is built into Samsung devices down to the hardware, supports the use of managed “containers” that allow businesses to separate personal information and apps on the device from the corporate information and apps. While having a good mobile policy in place for your employees is important, it won’t prevent a determined attacker. In the same sense that the last line of device recovery efforts provided by tracking tools such as Find My Mobile is necessary to buttress theft prevention efforts, fundamentally secure hardware and software thwart the attacks that good security practices can’t prevent.
In the end, it is the universal utility of smartphones that makes them invaluable to businesses, but also attractive to thieves and hackers. Mobile technology providers have come a long way in ensuring that businesses have the tools to keep their devices and data secure in the face of many threats — as long as you take some basic steps to adopt those tools.
Discover more solutions offered by Samsung tailored to support the success of SMBs. Then discover how Knox Manage can help you secure your growing mobile fleet.