You already know the basic rules of keeping your smartphone secure: make sure you regularly apply patches; have a lock code of at least six numbers; don’t click on spam; if you get a phishing message, delete it; and so on. But how about some more advanced advice to give you an extra edge against real threats?
Here are three next steps you can take to improve your mobile security against phone hackers.
1. Review your applications (and application stores)
Mixing sensitive information, such as personal financial data and private communications, with games and general browsing is never a good idea. Any application you install on your smartphone is a potential security problem, either because the developer is malicious or just because there’s a bug in the code. Only install applications from your vendor’s official application store, and even then, carefully choose what you add by checking the reputation of the application vendor. If you can’t resist having a jailbroken phone and pirating apps, grab another smartphone and let that be your playground.
The mobile security top 10
Get your free guide to better securing the personal and work data on your mobile phone. Download Now
At the same time, make sure you restrict the applications you do choose to download to their own small sandboxes. Then, applications must request access to other parts of your smartphone, such as contacts, locations and the camera. Periodically go into your settings and review which applications have access to which parts of your phone — and cut them off if there’s no longer a need. While you’re doing that, go ahead and delete any applications you have installed but are not using, like that travel guide to Amsterdam or the NCAA bracket app.
One final bit of advice on applications: use them in place of websites for important services. For example, if you have a bank account, credit card or investment account, whoever is providing financial services probably has an official app for your smartphone. Use it. When you connect your web browser to their websites, you’re opening up a large hole in your smartphone that hackers are especially keen to exploit. If you use an official app, it doesn’t mean there’s no hole, but you’re cutting out a lot of software you don’t need. That change alone reduces the risk of a malicious attacker taking control of your phone or stealing your data.
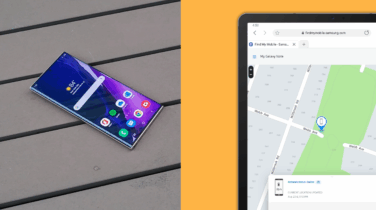
2. Remote wipe and remote lock your smartphone
If your smartphone is stolen, odds are the thief will immediately power it down and throw the SIM card in the trash. Usually, they’re not after your data; they want to wipe and sell your phone as quickly as possible. Usually — but not always. If the thief is careless or powers on the phone again, or if you just misplaced the phone, you want to be able to lock it and wipe the contents.
For Android devices, for example, you can log into your Google account and, if the device is set up properly, you can remotely lock and erase it. If your company has a Mobile Device Management (MDM) tool that has installed an agent on your phone, you or your company’s IT administrators can do the same thing (and perhaps more). However, this feature has to be enabled — just having a Google account connected to your phone isn’t enough to give you the ability to wipe it.
Take a few minutes to be sure that the remote wipe feature is enabled or that your IT administrators have the feature turned on. At the same time, make a practice run so you know how to call for a remote wipe. If your phone goes missing, you may only have a few minutes to send the command, so you should know exactly how to wipe (or ask your IT administrator to do it) before you need it.
3. Using public Wi-Fi? Get a VPN
Public Wi-Fi networks are a tremendous convenience, especially when traveling, but they’re also one of today’s most extensive security risks. When you connect to a public Wi-Fi network, you have absolutely no idea who is watching your traffic. Many, if not most, applications now use end-to-end encryption to reduce the window of vulnerability, but that’s not enough. For example, someone running a public Wi-Fi network can execute a man-in-the-middle (MITM) attack that redirects your connections to a malicious server that silently decrypts all your traffic as it flies by.
The solution is to use the public Wi-Fi for only one thing: to bring up a VPN tunnel to a trusted server, either at your company or a third-party VPN service. With the tunnel in place and covering 100 percent of your traffic, everything is encrypted and anonymous, and you’ve eliminated the possibility of an MITM attack. A quick web search for smartphone VPN services will turn up multiple competing vendors, or you can ask your IT administrator if the company VPN servers can handle this, too.
Your smartphone increasingly holds the keys to your most private and valuable data. Any action you can take to protect your data against phone hackers is a great investment you won’t regret making — and you might regret putting off.
Get a free guide to stopping security breaches in their tracks with an incident response playbook. Or, watch a video about using Samsung Knox to secure company data.