Businesses and organizations in every industry, from education to healthcare, are facing more cyberattacks than ever. That’s why it’s essential that they learn how to mitigate data security risk. In fact, 74% of organizations say their sensitive data was potentially compromised or breached at least once in the past year, according to a 2023 survey of security decision makers by Forrester Research.
These data breaches are also growing more expensive. The percentage of organizations that said they suffered a breach that cost $1 million or more over the past three years has risen from 27% to 36% in just a year, according to PricewaterhouseCoopers’s 2024 Global Digital Trust Insights survey. Furthermore, the Department of Homeland Security warns that financially motivated cyber threat actors are likely to impose significant financial costs on the U.S. economy in 2024 in its Homeland Threat Assessment 2024 report.
As security threats evolve, organizations must take a comprehensive, defense-in-depth approach to protect sensitive data and meet the latest data center security and privacy compliance requirements, particularly as they increasingly adopt cloud applications and hybrid workers arrangements, which expand the digital attack surface.
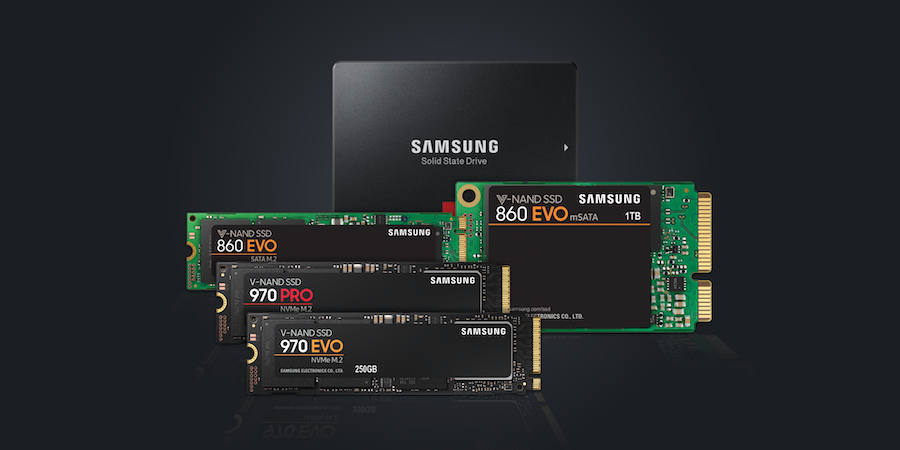
For organizations with on-premises data centers, defense starts with recognizing the top security risks for 2024 and seeking ways to mitigate them, including deploying solid state drives (SSDs) with built-in encryption.
Top data center security risks in 2024
Many of the cybersecurity concerns that have dominated the threat landscape in recent years remain today. However, they are evolving as cyberthieves apply new tools, angles and levels of sophistication. Learning how to mitigate data security risk means keeping an eye on these threats:
Ransomware
Cybercriminals are developing new methods of ransomware to extort organizations financially. New tactics include intermittent encryption or the partial encryption of files, which allows for faster encryption while reducing the chances of being detected, the Homeland Security report said.
Uncover the importance of SSD data security
Learn how SSDs protect sensitive company data with hardware-level data encryption. Download Now
Ransomware groups are also using multi-level extortion, in which they encrypt their victim’s data, threaten to publicly release the data, use distributed denial of service (DDoS) attacks and harass the victim’s customers to coerce the victim to pay, too.
In July, the Federal Bureau of Investigation also warned of two new ransomware tactics. Ransomware groups have begun to conduct multiple ransomware attacks on the same victim and employ data destruction methods to pressure victims to negotiate, the FBI said.
Social engineering and phishing attacks
Email hacking continues to be one of the costliest cybercrime activities, totaling $2.7 billion in 2022, the Homeland Security report found. Cybercriminals use social engineering or computer intrusion techniques to compromise email accounts and conduct unauthorized money transfers.
However, threat actors are going beyond email, engineering attacks using text messaging, collaboration tools and fake voicemail, according to Forrester. Some new social engineering attacks even include a CAPTCHA verification to look more legitimate.
Emerging AI-powered threats
The emergence of generative artificial intelligence (AI) and large language models will enable threat actors to develop and scale attacks in ways they couldn’t before.
For example, hackers can use generative AI to write more convincing phishing emails, as a CRN article pointed out. AI can also help create deepfake audio and video to fool victims into transfering funds, CRN said.
One emerging use case is using generative AI to sabotage the machine learning algorithms that organizations use in their software, such as email security software, by poisoning data and causing algorithmic drift, which weakens email detection efficacy. This type of AI cyberattack is still in its early days, though.
Staffing shortages and supply chain vulnerabilities
It’s difficult to maintain vigilance against threats when there is not enough trained people watching for them. Having an understaffed cybersecurity team raises vulnerability. Other data center security risks that organizations will continue to face in 2024 include insider threats and challenges in the software supply chain.
How to secure a data center from security threats
To safeguard data and data centers, businesses must take a multi-layered security approach. Some are adopting the Zero Trust Maturity Model promoted by the U.S. Cybersecurity & Infrastructure Security Agency, in which nothing is trusted inside or outside the network and strict access controls, user authentication and continuous monitoring are always maintained.
Encrypting data in production environments and their backups provides another layer of protection. Samsung SSDs — both Samsung PM9A3 NVMe PCIe SSD and Samsung PM893 SATA SSD — do this automatically, helping organizations protect their data with the strongest encryption algorithm available today .
Samsung PM9A3 SSD, designed for enterprise and large-scale cloud data centers, also keeps sensitive data protected with a secure boot feature that cryptographically verifies the integrity of every firmware image’s RSA digital signature prior to execution. This helps defend it against advanced security threats that target device firmware. Furthermore, Samsung data center SSDs are extremely reliable when it comes to protecting against data corruption in case of power failures.
As part of a broad security strategy, Samsung SSDs can help businesses mitigate data security risks, meet data center compliance regulations and bolster the security of their data centers.
Learn more about which Samsung SSD is right for your business and how to build a cyber incident response plan to enhance security against threats.