When it comes to corporate security, humans will be humans.
Consider the United Airlines flight attendant who recently posted a photo to the Internet including in clear view a sheet of paper with access codes to the cockpit door. Or the customer I spoke to recently at a sporting event who admitted keeping a laminated printout of all his IDs and passwords on his kitchen island at home. (Mitigating circumstances: these were personal not corporate accounts, and keeping such a list offline is at least safer than storing digitally.)
These are just two examples; every organization has its stories. My point here is that there is a fundamental tension between the need to keep valuable corporate assets secure and the reality that human beings have complicated and often chaotic lives. In other words, you are not a machine. A corporate security policy needs to acknowledge this fact. This is even more true when it comes to mobile phones, where work and life usage so often blurs.
You have friends, family and maybe even kids. Between working, socializing, exercising and traveling, you sometimes get distracted. Yes, you might even lose your phone in a taxi or let your three-year-old niece use your work phone to take a photo of that adorable crayon drawing.
Evaluate Your Security Plan
Discover if you have the right mobile security plan for your business. Download Now
You’re sometimes going to log into your account on unsecured public Wi-Fi systems because that’s the only way you can attempt to finish the 18 items on your to-do list over the next 45 minutes before your flight departs.
The whole point of mobile phone usage is to make your life a bit easier and more manageable. It’s supposed to simplify your life, rather than overcomplicate it. We think a lot about corporate security policy, and how to acknowledge the undeniable fact that humans will act like humans, which means we are a bit unpredictable, inconsistent and occasionally even make mistakes.
At the same time, employees need to understand that IT departments aren’t just trying to make your mobile phone usage difficult; they are trying to protect assets, even when you or your colleagues create a vulnerability.
Streamlining Security
To put it simply, the answer is to make our devices safe and secure even when humans have temporary lapses and expose security vulnerabilities.
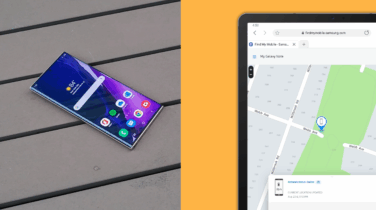
For example, our Knox security platform provides easy ways for you to separate work from life. So, if you do leave your phone in a cab, IT can wipe the apps and data stored in your Knox Workspace remotely. Through our data encryption and integration with a range of VPN solutions, we also have you covered when you connect to that “free WiFi” network in the coffee shop that it turns out is part of a man-in-the-middle hacking strategy.
The idea is to make business professionals more productive without expecting every employee to be a constant surrogate for corporate security. The Galaxy S8 takes this a step further by utilizing advanced biometrics instead of passwords to guard mobile devices. An iris scan is much safer than a password, because it is completely unique and impossible to misplace.
Early indications are that others are embracing our “let humans be humans” approach. “The fact that Knox exists and can be managed effectively and secured by existing EMM products is a big deal,” says Jack Gold, an analyst at J. Gold Associates. With this industry realization, we’re positive that not only will solutions like Knox and biometrics become best practice standards — they’ll let enterprises and their employees take the guesswork out of staying secure.
Learn more about how technology such as biometric scanning is changing the game for mobile security.