The “live trial” of large-scale federal telework that began in March due to COVID-19 is ongoing, but the results are clear: Telework has proven successful. More than half of all federal employees are connecting from home, including nearly 1 million Defense Department personnel.
Most agencies’ plans to bring everyone back into offices and facilities are fluid, though it appears likely that remote work will play a significant role going forward. Even the National Security Agency (NSA) fully expects teleworking to continue — and potentially expand — via a secure cloud environment.
Heading into a new government fiscal year, agency leaders have an unprecedented opportunity to reevaluate and expand their remote work strategies to ensure continued productivity. It’s also the ideal time to ensure the IT infrastructure and tools are adequately funded and ready to meet all business and mission requirements. But these strategies depend on several factors:
- Endpoint security
- Device deployment and management
- End-user productivity
In this three-part series, we’ll look at each of these in-depth, beginning with security.
More endpoints, greater risk
Security threats have grown dramatically during the pandemic. NASA Inspector General Paul Martin told a House subcommittee in September that since the pandemic began, “phishing attempts have doubled and malware attacks have increased exponentially.”
Many of these challenges stem from the sudden expansion of network endpoints. Bryan Ware, assistant director for cybersecurity for the Cybersecurity and Infrastructure Security Agency, put it this way: “The enterprise perimeter is now extended into a person’s home.” Basically, there’s more to protect.
Additionally, outdated or legacy platforms may simply not be up to the task, especially with regard to new cybersecurity requirements and privacy risks. Devices that worked well in the past may not be able to accept operating system (OS) upgrades or security patches. This makes sourcing new mobile platforms — smartphones and tablets that deliver full-featured computing power anywhere work happens — a viable alternative to aging desktops and laptops.

Smartphones as the centerpiece of your work-from-anywhere strategy
Mobile devices can replace laptops for many work situations — for field agents, depot and transportation personnel, flight line and motor pool maintenance, to name a few. But this means these devices not only need to be powerful computers; they need a level of security that aligns with government policy and practice.
With 300,000 agency-issued Samsung Galaxy devices in use today by federal personnel, security is fundamental, from the OS to the device to support for government-required authentication:
OS, maintenance and security releases
Smartphones must be updated regularly to defend against evolving threats. Inconsistent updates or carrier delays can leave devices vulnerable. Working closely with U.S. wireless carriers, Samsung’s turnaround time for Security Maintenance Releases (SMRs) is under 30 days on flagship smartphones, starting with the S10 and going forward. Samsung also guarantees three years of major OS updates from launch of a device, which extends the useful lifespan of Galaxy phones.
Enhance critical incident response with mobile
Learn how to execute safer, more effective incident response with a mobile-first approach. Download Now
Device security
Building on Android Enterprise, Samsung Knox provides defense-grade security that isolates, encrypts and secures the device from the chip up, enabling features such as malware protection and multifactor authentication, including advanced biometrics, mission action verification, cryptographic digital credentials and containerization. Samsung Knox 3.2 received 27 “strong” ratings out of 30 total ratings in Gartner’s May 2019 “Mobile OSs and Devices Security: A Comparison of Platforms” report. The latest version, Knox 3.6, includes additional enhancements to the security and customization functions of Galaxy phones and tablets, including advanced virtual private network (VPN) capabilities.
Samsung devices meet the most rigorous federal security standards and certifications, including National Institute of Standards and Technology (NIST), the Defense Information Systems Agency (DISA) Security Technical Implementation Guide (STIG) and National Information Assurance Partnership (NIAP) Common Criteria. Because of these critical security certifications, Samsung devices are listed on DISA’s APL (Approved Products List) and have also been approved by the NSA for classified deployments under the Commercial Solutions for Classified (CSfC) program.
Going further, Samsung’s exclusive Dual Data at Rest (DualDAR) encryption on the Galaxy S20 follows the NSA’s standard — dual encryption to enable the use of unclassified and classified use on the same device. DualDAR adds a critical layer of redundancy to Android OS file-based encryption (FBE) to further ensure agency data integrity, something no other smartphone manufacturer has accomplished. DualDAR is currently in use by over 75,000 Federal Galaxy S20 users.
Supply Chain Risk Management
Implementing precautions from production through delivery is essential. That’s why we employ and enforce a multilayer process to ensure compliance with strict standards, both internally and with our trading partners. Our comprehensive supply chain risk management (SCRM) program incorporates:
- Risk assessment and process standardization: Evaluating the sources and types of threats and how to adapt our strategies to combat them
- Physical security: Implementing and maintaining controls, from securing and monitoring facilities and containers to shipment tracking
- Employee vetting: Screening, training and ongoing security education for employees to ensure they’re qualified and trustworthy
- Cybersecurity: Data and system protection employing practices endorsed by the U.S. government and other governments to ensure end-to-end integrity
Samsung also partners with a range of government and private sector stakeholders on the Department of Homeland Security (DHS) Information and Communications Technology (ICT) Task Force. This is an essential part of our commitment to taking a leadership role in managing risk to the global ICT supply chain.
Device management
Depending on agency mission or business requirements, there may be situations where pushing a security or OS update to users’ devices needs to be scheduled for a later date. Using Samsung’s Knox E-FOTA solution, an agency’s IT management can monitor and control which patches are pushed to devices and when, ensuring that updates won’t interrupt critical operations across the agency.
Authentication and verification
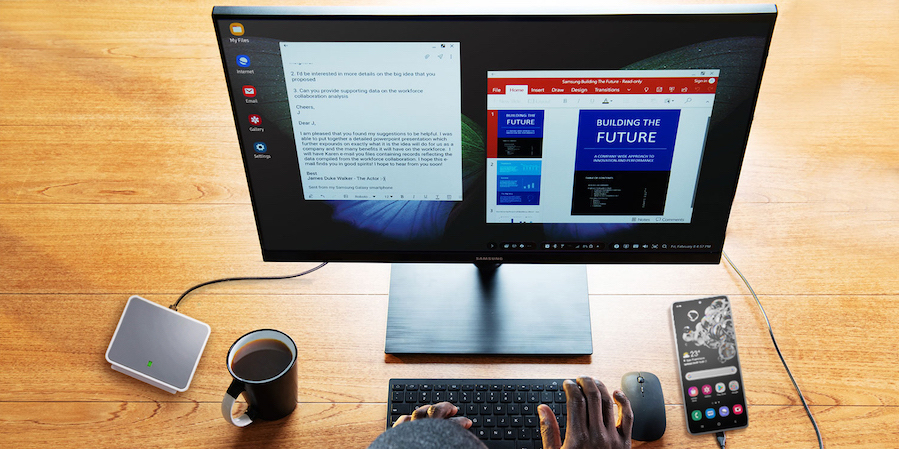
Samsung DeX — which lets personnel connect their Galaxy phones to a keyboard, mouse and monitor — also supports CAC/PIV readers to authenticate users, enabling logins from anywhere. And DeX enables virtual desktop infrastructure (VDI) solutions, adding another layer of protection.
The sheer volume of mobile employees — not only teleworkers but remote personnel whose jobs require them to work without a desk — has required agency IT leadership to redouble their efforts to keep everyone secure, connected and effective. As agencies focus on FY2021, mobility is certain to play a large role, so decisions about where to invest with a platform that ensures both greater productivity and unmatched security will be critical.
Learn how to enhance your agency’s remote security with Samsung Knox and Zero Trust in this free webinar. And find out more about how mobile technology can protect federal data.