With the explosion of mobile endpoints in the form of personal smartphones, IoT sensors and other connected devices, the threat surface area for cyber adversaries (both outsider and insider threats) to exploit government assets and networks is rapidly expanding. The 2018 Federal Cybersecurity Risk Determination Report and Action Plan reveals that at least 38 percent of federal cyber incidents did not have an identified attack vector in fiscal year 2016, indicating how difficult it can be for agencies to find and remediate such attacks.
As the use of mobile devices and services proliferate among civilians and military personnel, the Department of Defense (DoD) is focusing on how the agency can ramp up security without hampering productivity in an increasingly mobile technology ecosystem. As DoD CIO Dana Deasy explained in a recent FedScoop article, “One of the things I keep stressing is we have to step up and face the reality about the world around us becoming more and more mobile each and every day.”
In response to this trend, the department is developing an enterprise security strategy focused specifically on the devices workers use rather than traditional network perimeter security. This enterprise security strategy focuses on protecting devices and networks from both external and insider threats, and provides a framework that could potentially help shape how other agencies tackle similar challenges. In order for the DoD to enjoy the full benefits of mobility within this context, it’s important to dissect what it actually takes to strengthen security while still enabling an increasingly remote workforce.
Following are some strategies the DoD — and all federal agencies — should consider as they look to harden defenses and modernize their cybersecurity approaches.
Protecting Against Insider Threats With Identity Management
With a more complex threat environment, it’s more important than ever for the DoD to ensure users are who they say they are when accessing mobile devices and sensitive information. According to a recent GovLoop survey of federal employees, 61 percent report insider threats being a priority at their agencies, indicating that there is concern around organizations’ ability to accurately verify user access.
To better authenticate users, the DoD is slowly moving from the traditional common access card (CAC) to smartphones, which are already in the hands of every user and can more readily and securely work for identity, credentialing and access management. “I believe mobility is going to become ubiquitous, the devices out there are such that we’re going to have to move to a strategy of identity, credential and access management that moves us beyond the physical CAC,” Deasy said.
Transform Your Tactical Operations with Mobility
Discover how DoD is deploying mobile technologies to enhance and streamline tactical operations. Download Now
Tools like behavioral analytics layered into mobile solutions act to verify users according to biometric factors like irises and fingerprints, as well as by digital behavior like browsing habits, messaging syntax or how a user holds or interacts with a device. At least 50 percent of federal employees surveyed by GovLoop are turning to behavioral analytics as a primary strategy against insider threats. Mobile security features, such as the ability to geofence or remotely lock down a device, take things a step further to make a smartphone a compelling next-generation authentication solution.
Protecting Against Adversaries With Defense-Grade Security
To defend the DoD ecosystems against adversaries, an enterprise security strategy must layer defense-grade security built directly into mobile endpoints, whether they are smartphones or weapons systems, drones or other Internet of Things-connected sensors or devices.
An enterprise security strategy requires the ability to lock down a device from a potential cyberattack within seconds. This means devices must have sophisticated cybersecurity mechanisms built into the devices themselves. For example, defense-grade security solutions like Samsung Knox can secure mobile devices down to the hardware so data is protected, whether the user is in the office or in the field.
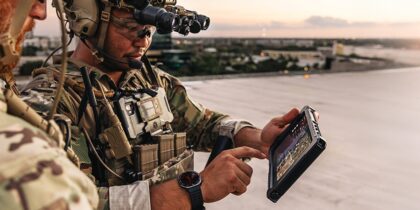
Additionally, mobile devices should be customizable for DoD missions, including tactical operations. Recently, in an effort to pursue a mobile-first strategy, the Defense Information Systems Agency (DISA) announced it will be using Samsung Galaxy S9 and S9+ smartphones, which have been approved for use with the DoD Mobility Unclassified Capability (DMUC). This tailored, mission-ready device has achieved the highest certification and security standards for classified communications and integrates easily into existing solutions to meet the specific needs of tactical operators, from calling in close air support to enhancing situational awareness.
DoD Strategy Is Helping Pave the Way for All of Government
The DoD has made significant advancements in securing traditional endpoints, but the introduction of nontraditional endpoints such as unmanned vehicles or drones continue to put pressure on IT. The DoD’s latest enterprise security strategy is a major step forward in helping to shape and inform best practices — not just across defense, but within all of government as endpoint threats continue to evolve and infiltrate agency systems.
Whether it’s securing a soldier’s wearable to monitor health and performance or protecting field data on a tablet used by civilian personnel, endpoint security will continue to challenge agencies as they address an increasingly connected and mobile workforce. Prioritizing stronger identity management, as well as deploying devices with built-in defense-grade security are essential next steps in helping the federal government adopt new transformative technologies in a secure way.
Discover how Samsung’s government technology solutions can assist agencies with their digital transformation.