As businesses increasingly rely on smartphones for their core productivity tools, securing and managing all those mobile devices, apps and data has become a growing challenge for IT teams.
On the security front, mobile devices by their very nature pose unique challenges — including greater risk of being lost or stolen — while the threat of mobile malware continues to increase in complexity and scope.
On the device management front, IT teams have been stretched thin by the mounting workload of supporting smartphones and tablets in addition to traditional PCs and infrastructure.
Even in organizations that have opted for a Bring Your Own Device (BYOD) approach to mobility, the responsibility has fallen on IT managers to ensure workers can safely access business apps and data on personal devices.
How Samsung Knox helps
To address both of these areas, Samsung has invested considerable resources in building out a full enterprise mobile security and management stack.
Introduced first on the Galaxy S4 in 2013, the Samsung Knox platform has set the standard for mobile security, receiving top ratings from industry analysts and certifications from multiple government agencies, including the U.S. Department of Defense.
Built on top of Knox’s platform-level security, Samsung also offers Knox Suite, an all-in-one solution to secure, deploy and manage mobile devices throughout their life cycle. Knox Suite bundles Knox Platform for Enterprise (KPE), Knox Mobile Enrollment (KME), Knox Manage, Knox Enterprise Firmware-Over-the-Air (E-FOTA) and, more recently, Knox Asset Intelligence (KAI)
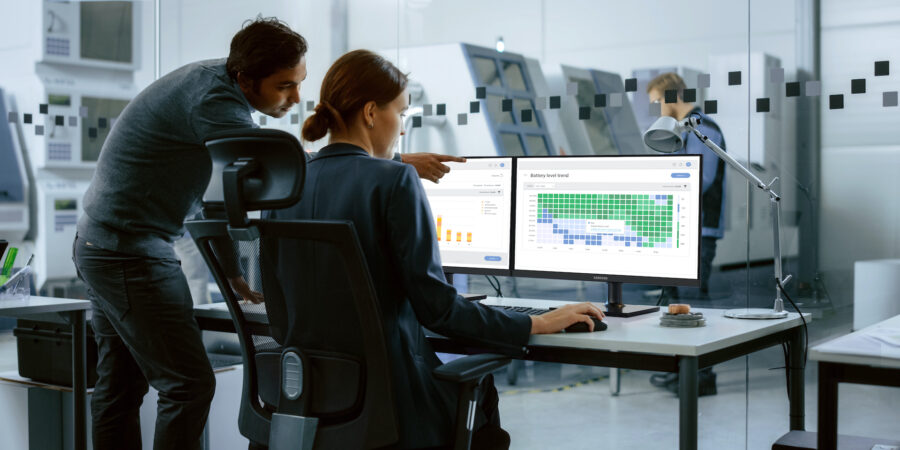
Solutions like Knox Manage and KPE provide IT departments powerful capabilities that can save time and avoid headaches associated with new mobile initiatives. Exclusive to Knox Suite, KAI is a cloud-based data analytics tool that provides extensive insight into your devices’ performance from the moment they’re deployed. IT teams can use this newfound visibility to prevent potential issues and address things protactively.
Here’s a more detailed rundown of the ways Knox can help you secure and manage your mobile deployment:
1. Hardware-based security
Samsung mobile devices are designed with security at the core. From the moment a phone or tablet first powers up, Samsung Knox provides defense-grade security that leverages processor architecture known as TrustZone to isolate sensitive computations and security certificates. If malware attempts to alter the kernel of the device’s OS, real-time checks will detect the change and immediately block access to sensitive data. This is the firm foundation on which the Knox security and management stack is built.
Samsung has continued to evolve its hardware-based security with Knox Vault, an isolated, tamper-proof subsystem with its own processor and memory. Knox Vault can protect sensitive data such as hardware-backed Android Keystore keys, biometric data and more. In addition to its dedicated, non-volatile secure storage, Knox Vault also controls access to keys by authenticating users, with longer login timeouts between authentication failures.
2. Advanced data protection
Enterprises in regulated industries with stringent security requirements can go above and beyond this foundation with KPE, which provides a robust set of features on top of the core Android Enterprise platform, filling security and management gaps and meeting the strict requirements.
KPE protects data at rest using sensitive data protection (SDP). Data is encrypted both when the device is locked and when it’s powered off. It provides further protection by allowing enterprise data to be isolated in secure app/data containers, such as Work Profile, which can be managed with security policies separately from the rest of the device.
KPE with Dual Data at Rest (DualDAR) adds two separate layers of encryption — an inner layer and an outer layer — to enable devices to be used in the most stringent of data security environments. And, because Knox DualDAR works on both BYOD and company-issued devices, IT admins can protect corporate data in any use case.
3. Simplified enrollment, management and firmware updates
In addition to close integration of Knox with third-party enterprise mobility management (EMM) solutions, Samsung offers its own affordable cloud-based EMM called Knox Manage.
Knox Manage makes EMM easy. From an intuitive cloud-based console, IT admins can remotely manage a fleet of devices to ensure company data is protected. Knox Manage also fulfills Google requirements in terms of Android Enterprise feature readiness. This includes core feature sets, advanced management, proven technical leadership and enterprise-level support. Market research firm IDC has recognized Knox Manage as a major player in endpoint management software.
Knox Manage provides:
- An easy-to-use quick start wizard for simple device setup
- Core controls you need to effectively manage your device fleet, including managing apps, content and device features such as connectivity
- Device management based on predefined events, such as blocking access to cameras on employee phones during work hours
- Ability to use Android Enterprise fully managed and work profile modes
- Full support of KPE, KME and Knox E-FOTA
- Real-time device monitoring enables location tracking (with employee consent) and messaging device owners without needing their phone numbers
If an employee encounters a problem while out of office, they can authorize IT admins to remotely access their device for easy troubleshooting. This allows IT admins to quickly help employees get back to work. And if a device is reported lost or stolen, IT can remotely locate it, lock it and wipe its content.
Samsung also provides an easy, surefire way to register new mobile devices in your EMM with KME, a free, zero-touch deployment service that allows you to automatically enroll devices the moment they power up. End users can skip setup wizards or additional account registrations to get up and running faster. With KME, you can ensure devices stay enrolled in corporate EMM systems. If an end user or malicious actor performs a factory reset or uninstalls the EMM agent from the device, KME will automatically reinitiate the enrollment process. Separately, IT can disable Android factory reset protection so that devices can be recovered even if credentials are lost. KME Direct, meanwhile, lets IT admins create an enrollment profile and send the user a QR code so they can set up their new devices on their own.
The Samsung tool set also includes Knox E-FOTA, which provides greater control over software updates, giving your business the power to validate, approve and deploy OS versions used across your device fleets. You can test and validate new firmware updates in advance to uncover potential compatibility issues between the new firmware and your business applications. You’re also in control of when your approved OS or security updates get rolled out to your enterprise’s mobile devices. Schedule deployments by device group and at a time of day that minimizes business disruption. Knox E-FOTA also allows you to set other criteria, including access to Wi-Fi connectivity and battery life, so that updates are quick and trouble-free.
Finally, Samsung can help organizations bolster their asset protection with Knox Guard, a cloud-based service that allows devices to be controlled remotely and even locked, so mobile carriers and banks can reduce their financial risks while running installment plans.
4. Custom configuration
As businesses look to use mobile devices to streamline specific business processes or perform specific functions, the need for custom configuration has grown. Knox Configure is a cloud-based solution developed to meet this need, enabling businesses to remotely configure any number of Samsung devices and tailor them to specific enterprise requirements. Configuration can include anything from custom branding of the booting UX, to preloading applications or shortcuts, to restricting access to certain features or creating a fully locked down experience limited to a single app.
Get your ultimate guide to Knox Configure
Learn how to optimize tablets for your unique business needs using Samsung Knox Configure. Download Now
Knox Configure lets you deploy the custom profile or “gold master image” right out of the box, so the device will automatically update to the latest configuration when the user first powers up.
5. Advanced biometrics
Relying solely on passwords or patterns to secure your mobile devices leaves them open to attack, which is why, for a complete smartphone security stack, enterprises should leverage biometric authentication to protect sensitive data. Samsung has been a leader in introducing highly secure biometric authentication options, including facial recognition, iris scanning and now the in-display ultrasonic fingerprint ID on newer Galaxy smartphones. Each of these biometric methods offers different advantages and levels of security, and should be evaluated based on your security and user requirements.
In addition to using biometrics to unlock the device itself, Samsung allows enterprises to leverage biometrics to protect secure on-device containers, as well as to replace credentials in other apps and websites using Samsung Pass. There’s also Continuous Multi-Factor Authentication (a feature in KPE), which repeatedly scans the user’s face and will lock the work profile if it detects someone unauthorized.
Defense-grade security for the enterprise
Today’s mobile-empowered workforce needs security that doesn’t get in the way of productivity. The Knox platform is engineered into Samsung devices at the manufacturing stage to enhance the Android platform for the enterprise. Knox keeps working to secure your device and data at all times, with security features to safeguard against risks when smartphones, tablets or wearables are powered off, during runtime and during the boot-up stage.
The Samsung Knox platform is the backbone of a full range of security solutions that enterprise IT administrators and developers can use to create, customize, deploy and manage purpose-built devices at scale.
Get started with MDM so your organization can spend less and do more — securely and efficiently — with this free interactive guide. And find out more about how Samsung Knox is setting a high bar for the most secure phone.